Содержание
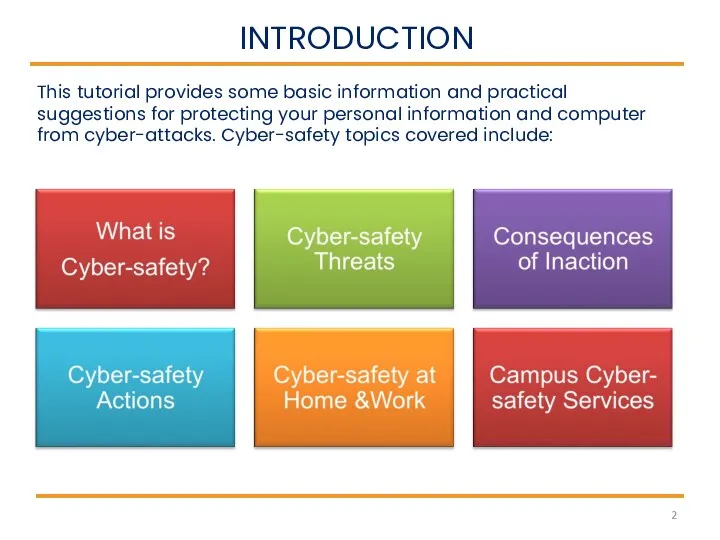
- 2. INTRODUCTION This tutorial provides some basic information and practical suggestions for protecting your personal information and
- 3. WHAT IS CYBER-SAFETY? Cyber-safety is a common term used to describe a set of practices, measures
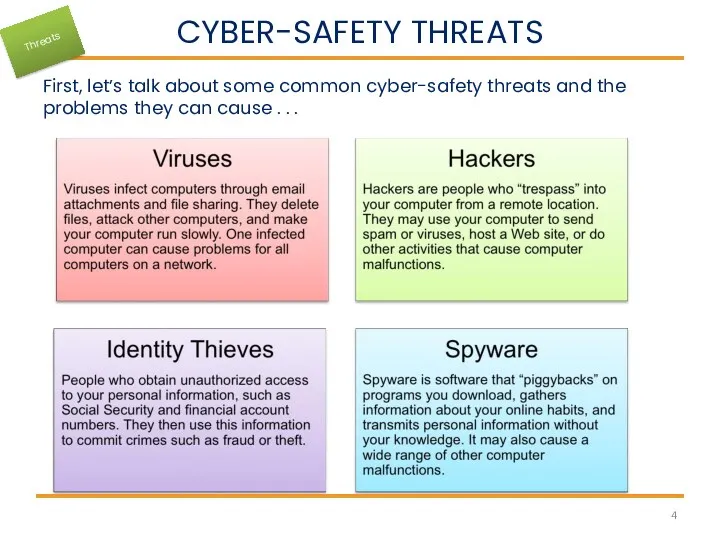
- 4. CYBER-SAFETY THREATS First, let’s talk about some common cyber-safety threats and the problems they can cause
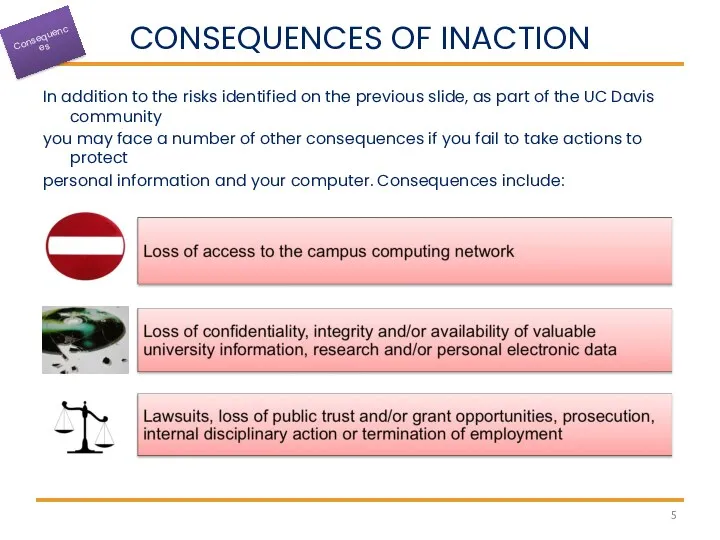
- 5. CONSEQUENCES OF INACTION In addition to the risks identified on the previous slide, as part of
- 6. CYBER-SAFETY ACTIONS The following slides describe the top seven actions you can take to protect personal
- 7. TOP SEVEN CYBER-SAFETY ACTIONS 1. Install OS/Software Updates 2. Run Anti-virus Software 3. Prevent Identity Theft
- 8. Updates-sometimes called patches-fix problems with your operating system (OS) (e.g., Windows XP, Windows Vista, Mac OS
- 9. Run Anti-Virus Software To avoid computer problems caused by viruses, install and run an anti-virus program
- 10. Prevent Identity Theft Don't give out financial account numbers, Social Security numbers, driver’s license numbers or
- 11. Turn on Personal Firewalls Check your computer's security settings for a built-in personal firewall. If you
- 12. Avoid Spyware/Adware Spyware and adware take up memory and can slow down your computer or cause
- 13. Protect Passwords Do not share your passwords, and always make new passwords difficult to guess by
- 14. Back Up Important Files Reduce your risk of losing important files to a virus, computer crash,
- 15. CYBER-SAFETY AT HOME Physically secure your computer by using security cables and locking doors and windows
- 16. CYBER-SAFETY AT WORK Be sure to work with your technical support coordinator before implementing new cyber-safety
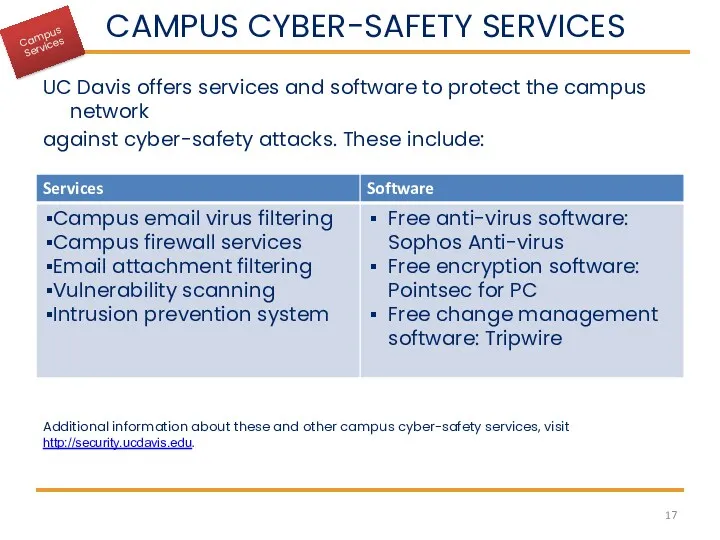
- 17. CAMPUS CYBER-SAFETY SERVICES UC Davis offers services and software to protect the campus network against cyber-safety
- 18. QUESTIONS? For more information about cyber-safety at UC Davis, visit http://security.ucdavis.edu. For answers to questions about
- 19. CYBER-SAFETY BASICS QUICK QUIZ True or False? Viruses can be transmitted via email, email attachments or
- 20. QUICK QUIZ ANSWERS True Identity thieves A and C are correct. D would probably help too,
- 21. ONE MORE THING . . . We want to hear from you! Send stories about your
- 22. REFERENCES UC Davis Cyber-safety Program policy (PPM 310-22) (http://manuals.ucdavis.edu/ppm/310/310-22.htm) UC Davis Cyber-safety Program (http://security.ucdavis.edu/cybersafety.cfm) UC Davis
- 24. Скачать презентацию
 Автоматизоване робоче місце інспектора з охорони праці
Автоматизоване робоче місце інспектора з охорони праці Введение в язык C#. Лекция 3-4
Введение в язык C#. Лекция 3-4 Системы управления базами данных (СУБД) Access
Системы управления базами данных (СУБД) Access Технология мультимедиа. Задания
Технология мультимедиа. Задания Программирование в Scratch. Игра Кот – обжора
Программирование в Scratch. Игра Кот – обжора Использование информационно-коммуникационных технологий на уроках русского языка н литературы. Курсовая работа
Использование информационно-коммуникационных технологий на уроках русского языка н литературы. Курсовая работа Введение. Сигналы. Классификация сигналов. Лекция 1
Введение. Сигналы. Классификация сигналов. Лекция 1 Сучасні веб-технології
Сучасні веб-технології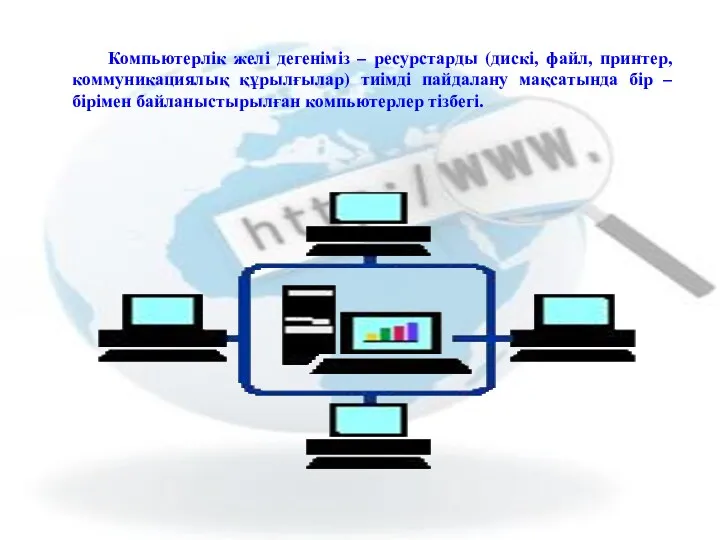 Компьютерлік желі дегеніміз ресурстарды. Дискі, файл, принтер, коммуникациялық құрылғылар
Компьютерлік желі дегеніміз ресурстарды. Дискі, файл, принтер, коммуникациялық құрылғылар Методи та системи паралельного програмування
Методи та системи паралельного програмування Технические средства компьютерной графики
Технические средства компьютерной графики Обзор и классификация систем подвижной радиосвязи
Обзор и классификация систем подвижной радиосвязи Понятие как форма мышления
Понятие как форма мышления Понятие ресурса ОС
Понятие ресурса ОС Использование компьютера в различных отраслях
Использование компьютера в различных отраслях Введение в конфигурирование в системе 1С:Предприятие 8. Основные объекты
Введение в конфигурирование в системе 1С:Предприятие 8. Основные объекты Измерение информации
Измерение информации Безопасность будущего (кибербезопасность)
Безопасность будущего (кибербезопасность) Алгоритмизация и программирование. Решение задач на компьютере
Алгоритмизация и программирование. Решение задач на компьютере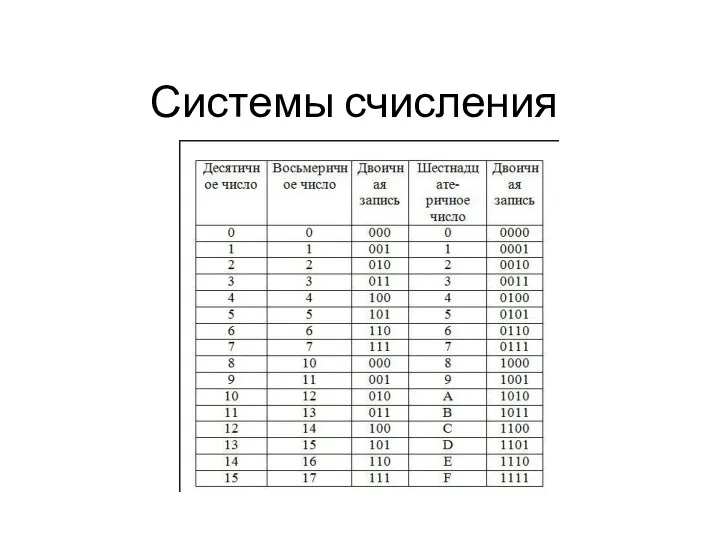 Системы счисления
Системы счисления Измерение информации
Измерение информации Материал к курсу лекций Matlab
Материал к курсу лекций Matlab Netiquette is the code of the user’s behaviour
Netiquette is the code of the user’s behaviour Использование пиксельных изображений в векторной графике и особенности работы с коллажами в Corel Draw
Использование пиксельных изображений в векторной графике и особенности работы с коллажами в Corel Draw Абсолютные, относительные и смешанные ссылки в электронных таблицах
Абсолютные, относительные и смешанные ссылки в электронных таблицах Организация ветвления. Циклы
Организация ветвления. Циклы Алгоритмы обработки массивов
Алгоритмы обработки массивов Компьютерные вирусы. Обзор и классификация компьютерных вирусов. Средства защиты от компьютерных вирусов
Компьютерные вирусы. Обзор и классификация компьютерных вирусов. Средства защиты от компьютерных вирусов