Содержание
- 2. STUDENT LEARNING OBJECTIVES Essentials of Management Information Systems Chapter 7 Securing Information Systems Why are information
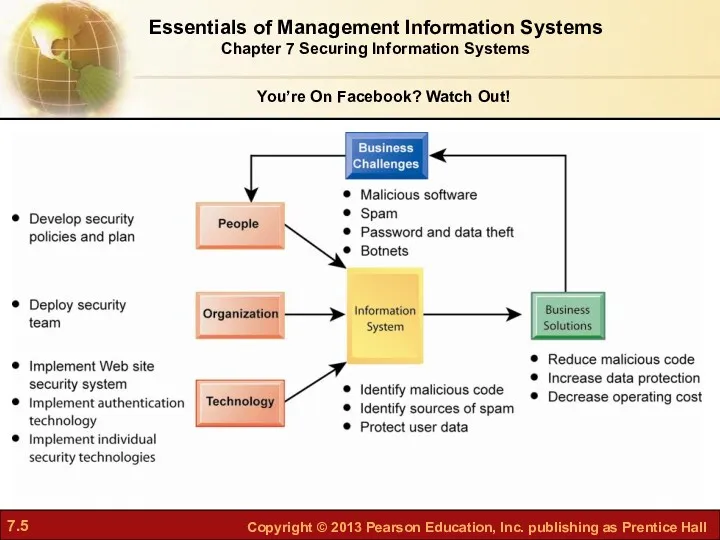
- 3. You’re On Facebook? Watch Out! Facebook—world’s largest social network Problem—Identity theft and malicious software 2009 18-month
- 4. Even with a dedicated security team and up-to-date security technology, Facebook is a target for hackers
- 5. Essentials of Management Information Systems Chapter 7 Securing Information Systems You’re On Facebook? Watch Out!
- 6. System Vulnerability and Abuse An unprotected computer connected to the Internet may be disabled within seconds
- 7. Why Systems Are Vulnerable Hardware problems Breakdowns, configuration errors, damage from improper use or crime Software
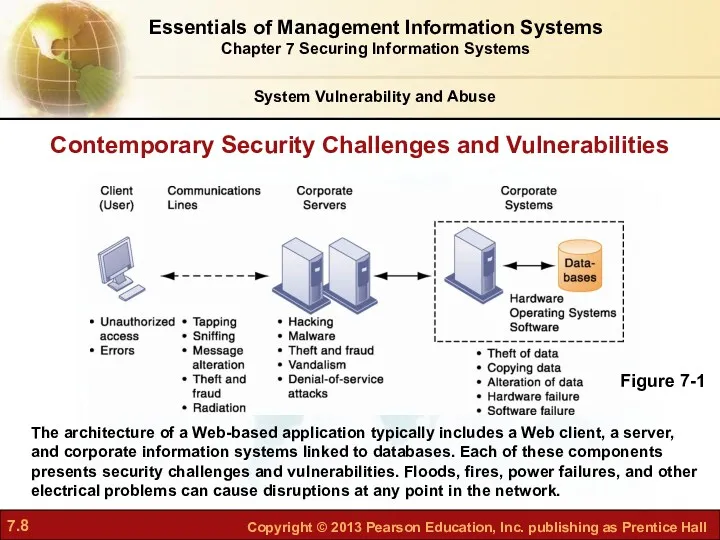
- 8. Contemporary Security Challenges and Vulnerabilities The architecture of a Web-based application typically includes a Web client,
- 9. Internet vulnerabilities Network open to anyone Size of Internet means abuses can have wide impact Use
- 10. Wireless security challenges Radio frequency bands easy to scan SSIDs (service set identifiers) Identify access points
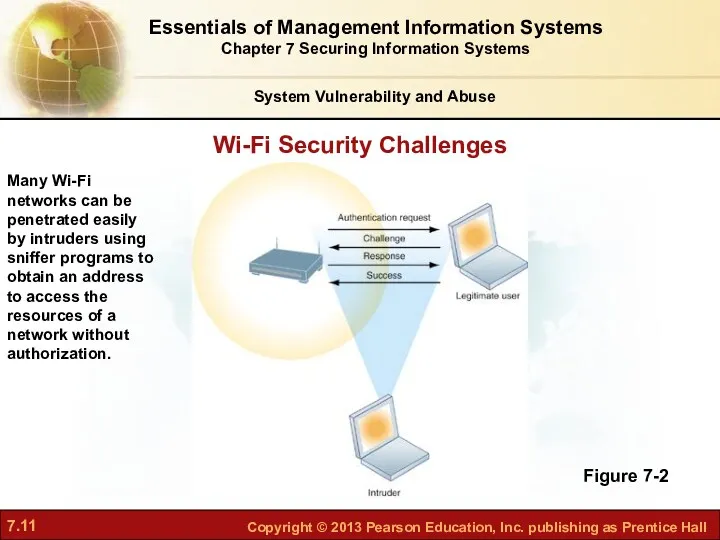
- 11. Wi-Fi Security Challenges Figure 7-2 Many Wi-Fi networks can be penetrated easily by intruders using sniffer
- 12. Malicious Software: Viruses, Worms, Trojan Horses, and Spyware Malware Viruses Rogue software program that attaches itself
- 13. Malicious Software: Viruses, Worms, Trojan Horses, and Spyware SQL injection attacks Spyware Small programs install themselves
- 14. Hackers and Computer Crime System Vulnerability and Abuse Hackers versus crackers Activities include: System intrusion Theft
- 15. Hackers and Computer Crime System Vulnerability and Abuse Spoofing Misrepresenting oneself by using fake e-mail addresses
- 16. Hackers and Computer Crime System Vulnerability and Abuse Denial-of-service attacks (DoS) Flooding server with thousands of
- 17. Hackers and Computer Crime System Vulnerability and Abuse Computer crime Any violations of criminal law that
- 18. Hackers and Computer Crime System Vulnerability and Abuse Identity theft Theft of personal information (social security
- 19. Hackers and Computer Crime System Vulnerability and Abuse Pharming Redirects users to a bogus Web page,
- 20. Read the Interactive Session and then discuss the following questions: Is cyberwarfare a serious problem? Why
- 21. Internal Threats: Employees Security threats often originate inside an organization Inside knowledge Sloppy security procedures User
- 22. Software Vulnerability System Vulnerability and Abuse Commercial software contains flaws that create security vulnerabilities Hidden bugs
- 23. Failed computer systems can lead to significant or total loss of business function Firms now more
- 24. Legal and Regulatory Requirements for Electronic Records Management Business Value of Security and Control Firms face
- 25. Electronic Evidence and Computer Forensics Evidence for white collar crimes often found in digital form Data
- 26. Establishing a Framework for Security and Control Information systems controls General controls Govern design, security, and
- 27. Establishing a Framework for Security and Control Types of general controls Software controls Hardware controls Computer
- 28. Establishing a Framework for Security and Control Application controls Specific controls unique to each computerized application,
- 29. Establishing a Framework for Security and Control Risk assessment Determines level of risk to firm if
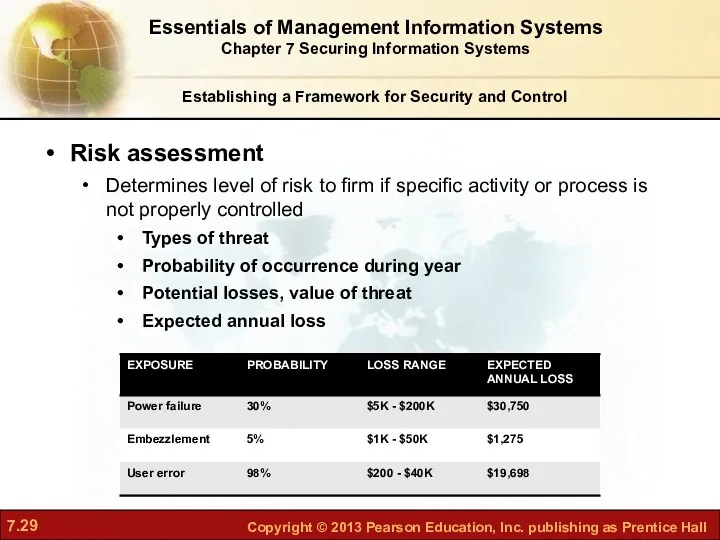
- 30. Establishing a Framework for Security and Control Security policy Ranks information risks Identifies acceptable security goals
- 31. Establishing a Framework for Security and Control Identity management Business process and technologies for identifying valid
- 32. Security Profiles for a Personnel System Figure 7-3 These two examples represent two security profiles or
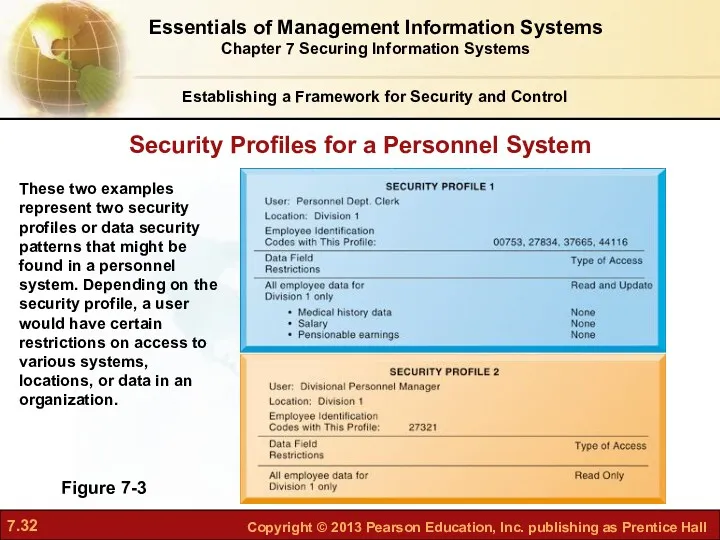
- 33. Establishing a Framework for Security and Control Disaster recovery planning: devises plans for restoration of disrupted
- 34. Establishing a Framework for Security and Control The Role of Auditing MIS audit Examines firm’s overall
- 35. Sample Auditor’s List of Control Weaknesses Figure 7-4 This chart is a sample page from a
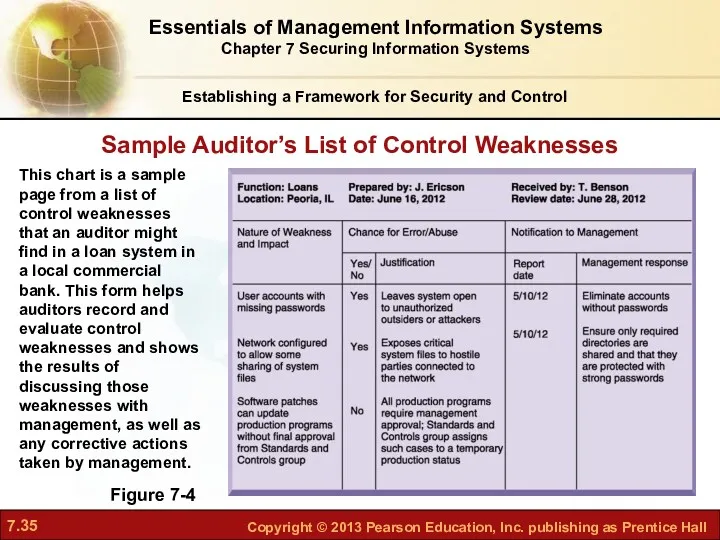
- 36. Identity Management and Authentication Technologies and Tools for Protecting Information Resources Authentication Password systems Tokens Smart
- 37. Firewall: Combination of hardware and software that prevents unauthorized access to network Technologies include: Packet filtering
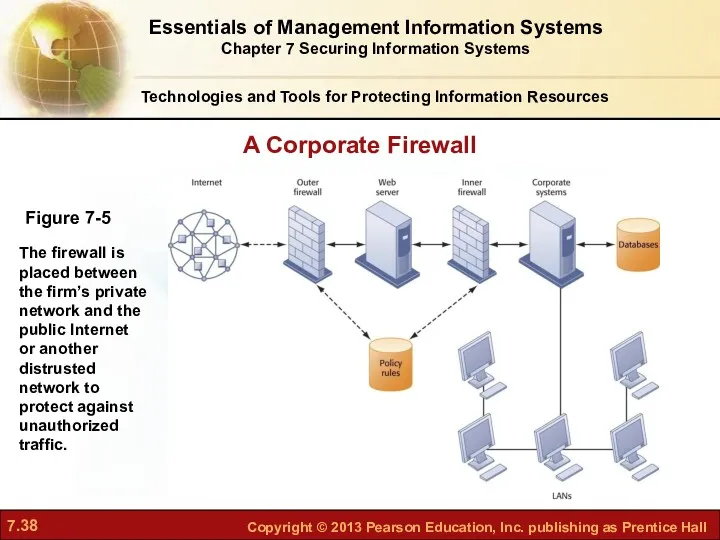
- 38. A Corporate Firewall Figure 7-5 The firewall is placed between the firm’s private network and the
- 39. Intrusion detection systems: Monitor hot spots on corporate networks to detect and deter intruders Examine events
- 40. WEP security can be improved by: Activating it Assigning unique name to network’s SSID Using it
- 41. Encryption: Transforming text or data into cipher text that cannot be read by unintended recipients Two
- 42. Two methods of encryption Symmetric key encryption Sender and receiver use single, shared key Public key
- 43. Public Key Encryption Figure 7-6 A public key encryption system can be viewed as a series
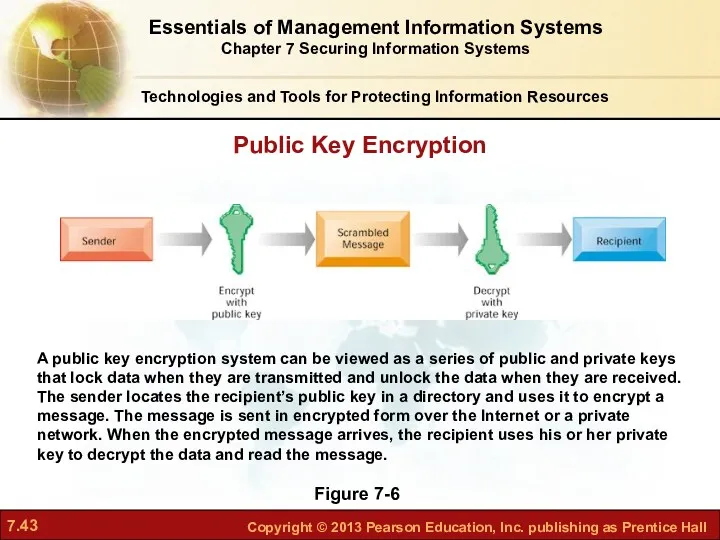
- 44. Digital certificate: Data file used to establish the identity of users and electronic assets for protection
- 45. Digital Certificates Figure 7-7 Digital certificates help establish the identity of people or electronic assets. They
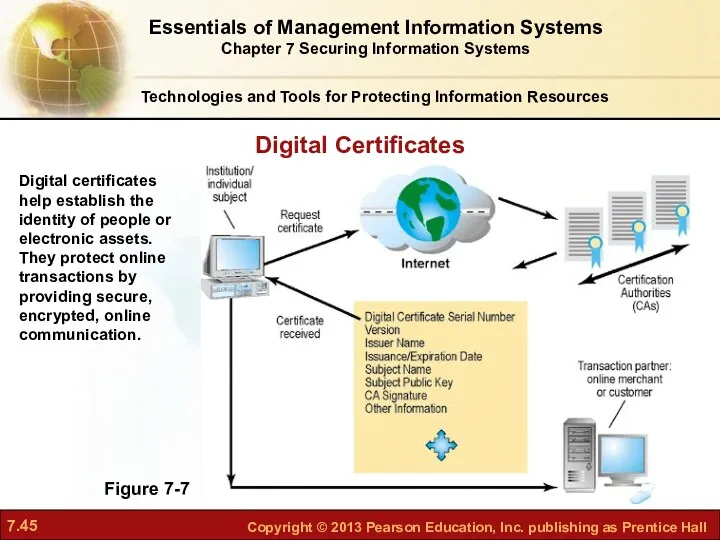
- 46. Online transaction processing requires 100% availability, no downtime Fault-tolerant computer systems For continuous availability, e.g., stock
- 47. Recovery-oriented computing Designing systems that recover quickly with capabilities to help operators pinpoint and correct faults
- 48. Security Issues for Cloud Computing and the Mobile Digital Platform Essentials of Management Information Systems Chapter
- 49. Software Metrics: objective assessments of system in form of quantified measurements, examples include? Number of transactions
- 50. Interactive Session: Technology How Secure Is Your Smartphone? Read the Interactive Session and then discuss the
- 52. Скачать презентацию
 Работа на теплоходе
Работа на теплоходе Аналоговые и цифровые системы коммутации
Аналоговые и цифровые системы коммутации Моя малая родина Йошкар-Ола
Моя малая родина Йошкар-Ола Химия глин и принципы ингибирования глинистых пород
Химия глин и принципы ингибирования глинистых пород Игровая програма: Вместе весело играть
Игровая програма: Вместе весело играть Мұнай өндірісіндегі цементтің қолданылуы
Мұнай өндірісіндегі цементтің қолданылуы Презентация к родительскому собранию на тему Мама, папа,я - читающая семья
Презентация к родительскому собранию на тему Мама, папа,я - читающая семья Шпон, фанера и композитные материалы
Шпон, фанера и композитные материалы Ступенька в будущее
Ступенька в будущее Знакомство с Красной книгой 1-3 классы.
Знакомство с Красной книгой 1-3 классы. Родительское собрание в 3 классе Ваш ребенок - третьеклассник
Родительское собрание в 3 классе Ваш ребенок - третьеклассник День гимназиста
День гимназиста Неотложные состояния в оториноларингологии
Неотложные состояния в оториноларингологии Электрические цепи. Последовательное и параллельное соединения проводников
Электрические цепи. Последовательное и параллельное соединения проводников внеклассное мероприятие в 11 классе смертная казнь: за или против
внеклассное мероприятие в 11 классе смертная казнь: за или против Пожарные аварийно-спасательные автомобили
Пожарные аварийно-спасательные автомобили В мире цветов
В мире цветов Ключевые бизнес-процессы в организации
Ключевые бизнес-процессы в организации Основные компоненты компьютера и их функции
Основные компоненты компьютера и их функции Морфемика и словообразование
Морфемика и словообразование Формування телевізійного сигналу
Формування телевізійного сигналу Автотранспорт. Большегрузные автоперевозки
Автотранспорт. Большегрузные автоперевозки История развития робототехники
История развития робототехники Органические молекулы – углеводы, жиры, липоиды
Органические молекулы – углеводы, жиры, липоиды Исследовательская работа Осенние листья
Исследовательская работа Осенние листья Қазақ халқының психологиясы
Қазақ халқының психологиясы Что такое почва
Что такое почва Парадоксы жизни
Парадоксы жизни