Содержание
- 2. Principles of cryptography
- 3. Friends and enemies: Alice, Bob, Trudy well-known in network security world Bob, Alice (lovers!) want to
- 4. 8: Network Security 8- Who might Bob, Alice be? … well, real-life Bobs and Alices! Web
- 5. 8: Network Security 8- There are bad guys (and girls) out there! Q: What can a
- 6. Cryptography 8: Network Security 8-
- 7. 8: Network Security 8-
- 8. 8: Network Security 8-
- 9. 8: Network Security 8-
- 12. 8: Network Security 8-
- 13. 8: Network Security 8-
- 14. 8: Network Security 8-
- 15. 8: Network Security 8-
- 16. 8: Network Security 8-
- 17. 8: Network Security 8-
- 18. 8: Network Security 8-
- 19. 8: Network Security 8-
- 20. 8: Network Security 8-
- 21. 8: Network Security 8-
- 22. 8: Network Security 8-
- 23. 8: Network Security 8-
- 24. 8: Network Security 8-
- 25. 8: Network Security 8-
- 26. 8: Network Security 8-
- 27. 8: Network Security 8-
- 28. 8: Network Security 8-
- 29. 8: Network Security 8-
- 30. 8: Network Security 8-
- 31. 8: Network Security 8-
- 48. gcd(k,26)=1
- 94. 8: Network Security 8- The language of cryptography symmetric key crypto: sender, receiver keys identical public-key
- 95. 8: Network Security 8- Symmetric key cryptography substitution cipher: substituting one thing for another monoalphabetic cipher:
- 96. 8: Network Security 8- Symmetric key cryptography symmetric key crypto: Bob and Alice share know same
- 97. 8: Network Security 8-
- 98. 8: Network Security 8-
- 136. 8: Network Security 8- Symmetric key crypto: DES initial permutation 16 identical “rounds” of function application,
- 146. 8: Network Security 8-
- 147. 8: Network Security 8-
- 148. 8: Network Security 8-
- 149. 8: Network Security 8-
- 150. 8: Network Security 8-
- 151. 8: Network Security 8-
- 152. 8: Network Security 8-
- 153. 8: Network Security 8-
- 154. 8: Network Security 8-
- 155. 8: Network Security 8-
- 156. 8: Network Security 8-
- 157. 8: Network Security 8-
- 158. 8: Network Security 8-
- 159. 8: Network Security 8- The language of cryptography symmetric key crypto: sender, receiver keys identical public-key
- 160. 8: Network Security 8- Symmetric key cryptography substitution cipher: substituting one thing for another monoalphabetic cipher:
- 161. 8: Network Security 8- Symmetric key cryptography symmetric key crypto: Bob and Alice share know same
- 162. 8: Network Security 8- Symmetric key crypto: DES DES: Data Encryption Standard US encryption standard [NIST
- 163. 8: Network Security 8- Symmetric key crypto: DES initial permutation 16 identical “rounds” of function application,
- 164. 8: Network Security 8- AES: Advanced Encryption Standard new (Nov. 2001) symmetric-key NIST standard, replacing DES
- 165. 8: Network Security 8- Block Cipher one pass through: one input bit affects eight output bits
- 166. 8: Network Security 8- Cipher Block Chaining cipher block: if input block repeated, will produce same
- 167. 8: Network Security 8- Public key cryptography symmetric key crypto requires sender, receiver know shared secret
- 168. 8: Network Security 8- Public key cryptography plaintext message, m ciphertext encryption algorithm decryption algorithm Bob’s
- 169. 8: Network Security 8- Public key encryption algorithms need K ( ) and K ( )
- 170. 8: Network Security 8- RSA: Choosing keys 1. Choose two large prime numbers p, q. (e.g.,
- 171. 8: Network Security 8- RSA: Encryption, decryption 0. Given (n,e) and (n,d) as computed above 2.
- 172. 8: Network Security 8- RSA example: Bob chooses p=5, q=7. Then n=35, z=24. e=5 (so e,
- 173. 8: Network Security 8- RSA: Why is that Useful number theory result: If p,q prime and
- 174. 8: Network Security 8- RSA: another important property The following property will be very useful later:
- 175. 8: Network Security 8- Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography
- 176. 8: Network Security 8- Message Integrity Bob receives msg from Alice, wants to ensure: message originally
- 177. 8: Network Security 8- Internet checksum: poor crypto hash function Internet checksum has some properties of
- 178. 8: Network Security 8- Message Authentication Code s (shared secret) (message) s (shared secret)
- 179. 8: Network Security 8- MACs in practice MD5 hash function widely used (RFC 1321) computes 128-bit
- 180. 8: Network Security 8- Digital Signatures cryptographic technique analogous to hand-written signatures. sender (Bob) digitally signs
- 181. 8: Network Security 8- Digital Signatures simple digital signature for message m: Bob “signs” m by
- 182. 8: Network Security 8- Digital Signatures (more) suppose Alice receives msg m, digital signature KB(m) Alice
- 183. 8: Network Security 8- H(m) Bob’s private key Bob sends digitally signed message: Alice verifies signature
- 184. 8: Network Security 8- Public Key Certification public key problem: When Alice obtains Bob’s public key
- 185. 8: Network Security 8- Certification Authorities Certification Authority (CA): binds public key to particular entity, E.
- 186. 8: Network Security 8- Certification Authorities when Alice wants Bob’s public key: gets Bob’s certificate (Bob
- 187. 8: Network Security 8- A certificate contains: Serial number (unique to issuer) info about certificate owner,
- 188. 8: Network Security 8- Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography
- 189. 8: Network Security 8- Authentication Goal: Bob wants Alice to “prove” her identity to him Protocol
- 190. 8: Network Security 8- Authentication Goal: Bob wants Alice to “prove” her identity to him Protocol
- 191. 8: Network Security 8- Authentication: another try Protocol ap2.0: Alice says “I am Alice” in an
- 192. 8: Network Security 8- Authentication: another try Protocol ap2.0: Alice says “I am Alice” in an
- 193. 8: Network Security 8- Authentication: another try Protocol ap3.0: Alice says “I am Alice” and sends
- 194. 8: Network Security 8- Authentication: another try Protocol ap3.0: Alice says “I am Alice” and sends
- 195. 8: Network Security 8- Authentication: yet another try Protocol ap3.1: Alice says “I am Alice” and
- 196. 8: Network Security 8- Authentication: another try Protocol ap3.1: Alice says “I am Alice” and sends
- 197. 8: Network Security 8- Authentication: yet another try Goal: avoid playback attack Failures, drawbacks? Nonce: number
- 198. 8: Network Security 8- Authentication: ap5.0 ap4.0 requires shared symmetric key can we authenticate using public
- 199. 8: Network Security 8- ap5.0: security hole Man (woman) in the middle attack: Trudy poses as
- 200. 8: Network Security 8- ap5.0: security hole Man (woman) in the middle attack: Trudy poses as
- 201. 8: Network Security 8- Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography
- 202. 8: Network Security 8- Secure e-mail Alice: generates random symmetric private key, KS. encrypts message with
- 203. 8: Network Security 8- Secure e-mail Bob: uses his private key to decrypt and recover KS
- 204. 8: Network Security 8- Secure e-mail (continued) Alice wants to provide sender authentication message integrity. Alice
- 205. 8: Network Security 8- Secure e-mail (continued) Alice wants to provide secrecy, sender authentication, message integrity.
- 206. 8: Network Security 8- Pretty good privacy (PGP) Internet e-mail encryption scheme, de-facto standard. uses symmetric
- 207. 8: Network Security 8- Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography
- 208. 8: Network Security 8- Secure sockets layer (SSL) provides transport layer security to any TCP-based application
- 209. 8: Network Security 8- SSL: three phases 1. Handshake: Bob establishes TCP connection to Alice authenticates
- 210. 8: Network Security 8- SSL: three phases 2. Key Derivation: Alice, Bob use shared secret (MS)
- 211. 8: Network Security 8- SSL: three phases 3. Data transfer MB b1b2b3 … bn d EB
- 212. 8: Network Security 8- Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography
- 213. 8: Network Security 8- IPsec: Network Layer Security network-layer secrecy: sending host encrypts the data in
- 214. 8: Network Security 8- Authentication Header (AH) Protocol provides source authentication, data integrity, no confidentiality AH
- 215. 8: Network Security 8- ESP Protocol provides secrecy, host authentication, data integrity. data, ESP trailer encrypted.
- 216. 8: Network Security 8- Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography
- 217. 8: Network Security 8- IEEE 802.11 security war-driving: drive around Bay area, see what 802.11 networks
- 218. 8: Network Security 8- Wired Equivalent Privacy (WEP): authentication as in protocol ap4.0 host requests authentication
- 219. 8: Network Security 8- WEP data encryption host/AP share 40 bit symmetric key (semi-permanent) host appends
- 220. 8: Network Security 8- 802.11 WEP encryption Sender-side WEP encryption
- 221. 8: Network Security 8- Breaking 802.11 WEP encryption security hole: 24-bit IV, one IV per frame,
- 222. 8: Network Security 8- 802.11i: improved security numerous (stronger) forms of encryption possible provides key distribution
- 223. 8: Network Security 8- AP: access point AS: Authentication server wired network STA: client station STA
- 224. 8: Network Security 8- wired network EAP TLS EAP EAP over LAN (EAPoL) IEEE 802.11 RADIUS
- 225. 8: Network Security 8- Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography
- 226. 8: Network Security 8- Firewalls isolates organization’s internal net from larger Internet, allowing some packets to
- 227. 8: Network Security 8- Firewalls: Why prevent denial of service attacks: SYN flooding: attacker establishes many
- 228. 8: Network Security 8- Stateless packet filtering internal network connected to Internet via router firewall router
- 229. 8: Network Security 8- Stateless packet filtering: example example 1: block incoming and outgoing datagrams with
- 230. 8: Network Security 8- Stateless packet filtering: more examples
- 231. 8: Network Security 8- Access Control Lists ACL: table of rules, applied top to bottom to
- 232. 8: Network Security 8- Stateful packet filtering stateless packet filter: heavy handed tool admits packets that
- 233. 8: Network Security 8- Stateful packet filtering ACL augmented to indicate need to check connection state
- 234. 8: Network Security 8- Application gateways filters packets on application data as well as on IP/TCP/UDP
- 235. 8: Network Security 8- Limitations of firewalls and gateways IP spoofing: router can’t know if data
- 236. 8: Network Security 8- Intrusion detection systems packet filtering: operates on TCP/IP headers only no correlation
- 237. 8: Network Security 8- Web server FTP server DNS server application gateway Internet demilitarized zone internal
- 239. Скачать презентацию
 Mixed conditionals
Mixed conditionals Places. Houses
Places. Houses My school day. What school do you go to?
My school day. What school do you go to? Home reading “Wishing well”
Home reading “Wishing well” Events breaking the law
Events breaking the law What Is Organizational Behavior
What Is Organizational Behavior Philosophy of Existentialism
Philosophy of Existentialism New years resolutions
New years resolutions Instructions for presentation
Instructions for presentation English inscription on clothes
English inscription on clothes How to Identify a Shopaholic
How to Identify a Shopaholic Singular and Plural. One and More. 6 класс
Singular and Plural. One and More. 6 класс Викторина по английскому языку для учащихся 6-х классов “Do you know Britain well?”
Викторина по английскому языку для учащихся 6-х классов “Do you know Britain well?” Hobbies and interests
Hobbies and interests Presentation about building materials. OSB plate
Presentation about building materials. OSB plate How much. How many. I have plenty of time
How much. How many. I have plenty of time Great Britain
Great Britain Sport in our life
Sport in our life Ielts writing task I. How to describe a map
Ielts writing task I. How to describe a map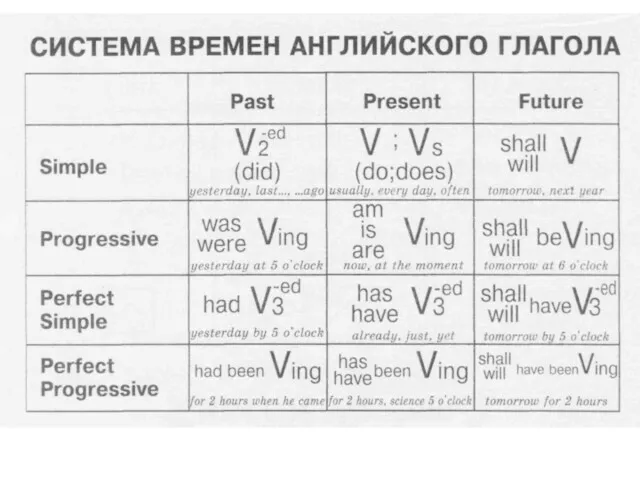 Система времен английского глагола
Система времен английского глагола Alphabet. Английский алфавит
Alphabet. Английский алфавит Prepositions of Place
Prepositions of Place Nature Magic: Web of Life
Nature Magic: Web of Life Знакомство с новой лексикой. Урок 40.2
Знакомство с новой лексикой. Урок 40.2 My profession is an auto mechanic. Professional skills
My profession is an auto mechanic. Professional skills Dream the room
Dream the room How to shop properly?
How to shop properly? English in Use. Spotlight 8
English in Use. Spotlight 8