Содержание
- 2. 1.1 What is SQL injection? UNDERSTANDING SQL INJECTION Define SQL injection. UNDERSTANDING HOW IT HAPPENS 1.2
- 3. SQL injection Web applications are becoming more sophisticated and increasingly technically complex. SQL injection is
- 4. SQL injection sample To illustrate this, let’s return to the previous example of a simple online
- 5. SQL injection simple example The URL examples in this chapter use GET parameters instead of POST
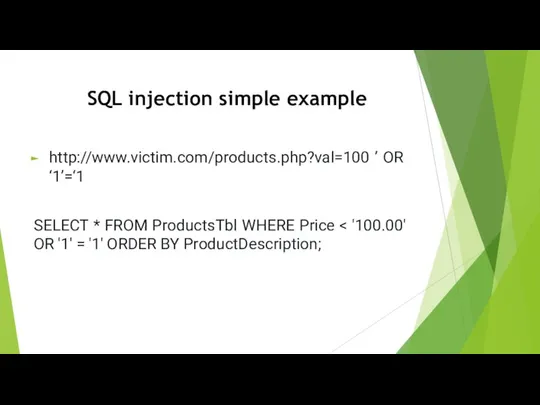
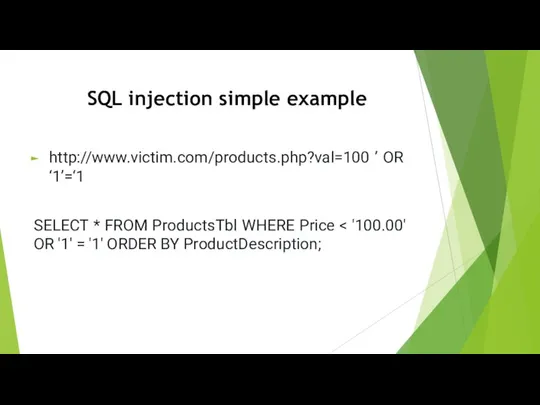
- 6. http://www.victim.com/products.php?val=100 ’ OR ‘1’=‘1 SELECT * FROM ProductsTbl WHERE Price SQL injection simple example
- 7. http://www.victim.com/products.php?val=100 ’ OR ‘1’=‘1 SELECT * FROM ProductsTbl WHERE Price SQL injection simple example
- 8. Example of the SQL injection for CMS A CMS is a Web application that is used
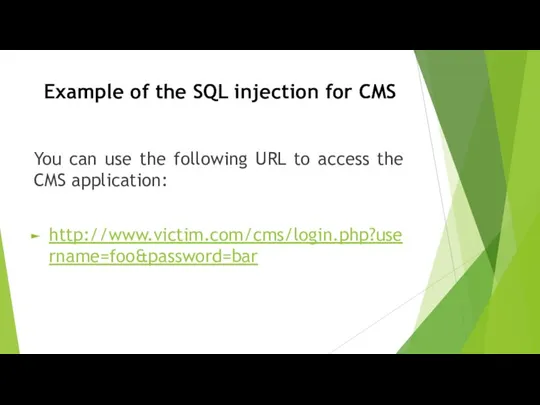
- 9. Example of the SQL injection for CMS You can use the following URL to access the
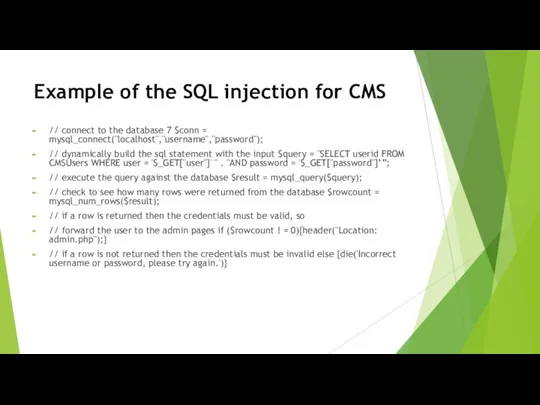
- 10. Example of the SQL injection for CMS // connect to the database 7 $conn = mysql_connect("localhost","username","password");
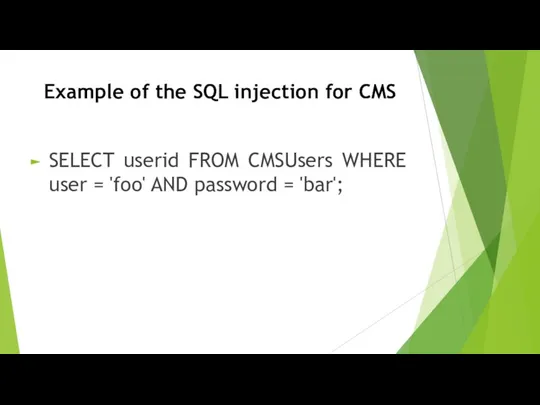
- 11. Example of the SQL injection for CMS SELECT userid FROM CMSUsers WHERE user = 'foo' AND
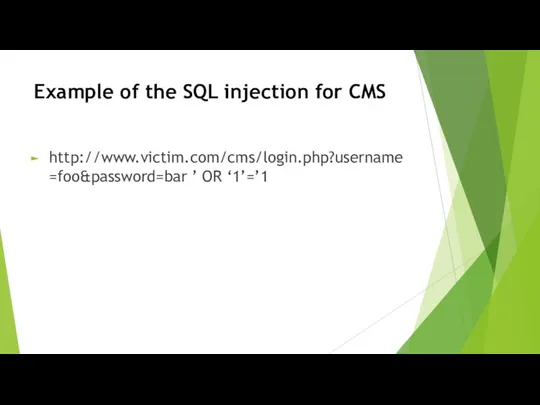
- 12. Example of the SQL injection for CMS http://www.victim.com/cms/login.php?username=foo&password=bar ’ OR ‘1’=’1
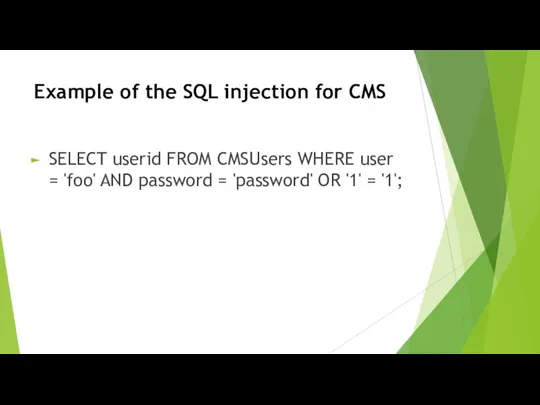
- 13. Example of the SQL injection for CMS SELECT userid FROM CMSUsers WHERE user = 'foo' AND
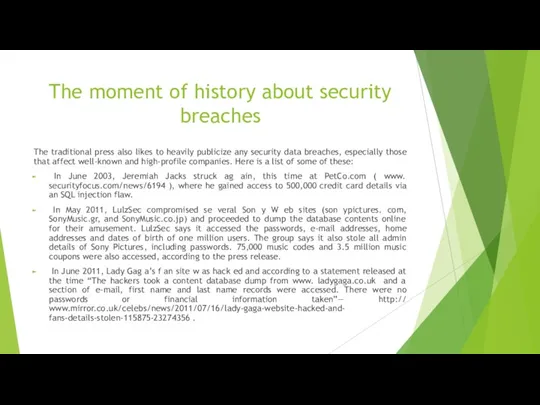
- 14. The moment of history about security breaches The traditional press also likes to heavily publicize any
- 15. UNDERSTANDING HOW IT HAPPENS SQL injection SQL is the standard language for accessing Microsoft SQL Server,
- 16. Variety of SQL injection There are a wide variety of SQL injection vulnerabilities, attacks, and techniques,
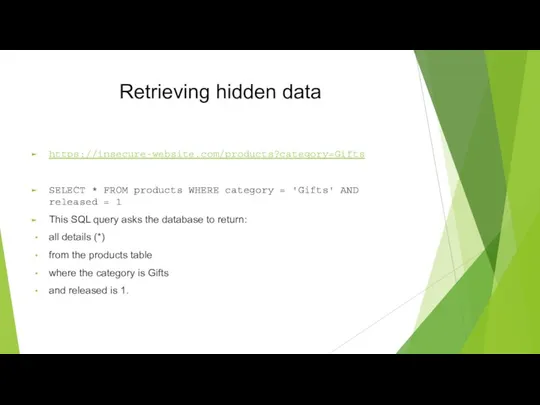
- 17. Retrieving hidden data https://insecure-website.com/products?category=Gifts SELECT * FROM products WHERE category = 'Gifts' AND released = 1
- 18. Retrieving hidden data The restriction released = 1 is being used to hide products that are
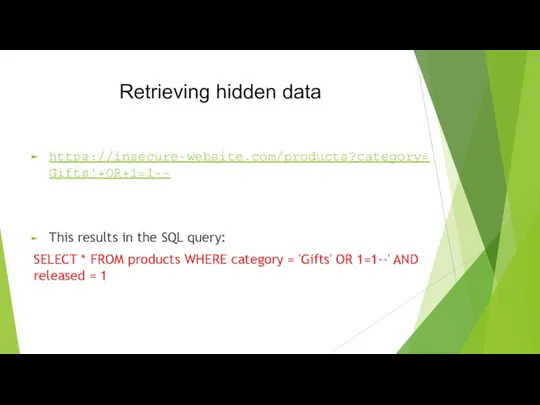
- 19. Retrieving hidden data https://insecure-website.com/products?category=Gifts'+OR+1=1-- This results in the SQL query: SELECT * FROM products WHERE category
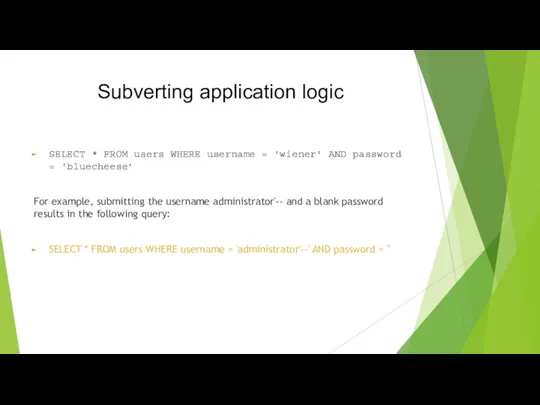
- 20. Subverting application logic SELECT * FROM users WHERE username = 'wiener' AND password = 'bluecheese’ For
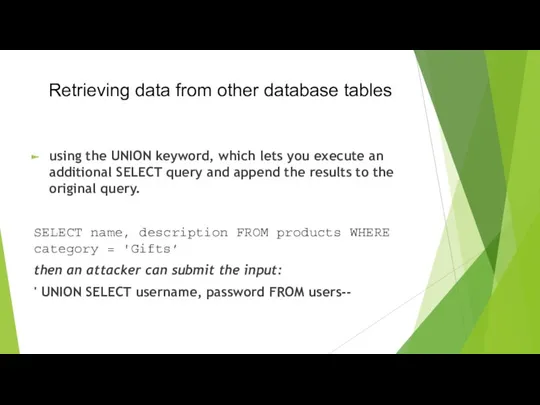
- 21. Retrieving data from other database tables using the UNION keyword, which lets you execute an additional
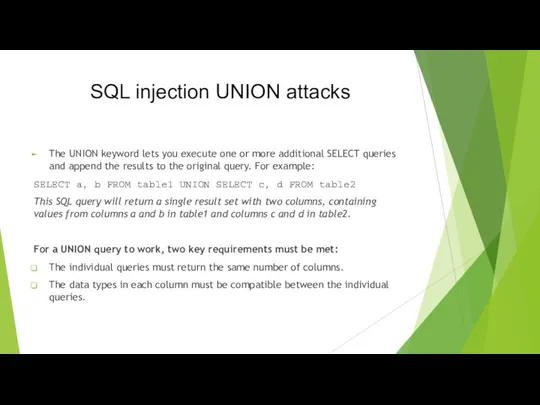
- 22. SQL injection UNION attacks The UNION keyword lets you execute one or more additional SELECT queries
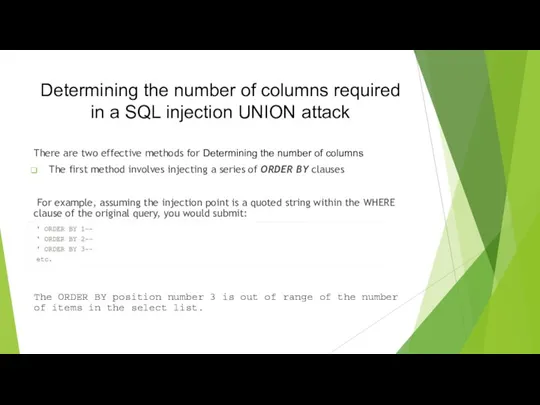
- 23. Determining the number of columns required in a SQL injection UNION attack There are two effective
- 24. Determining the number of columns required in a SQL injection UNION attack The second method involves
- 25. Finding columns with a useful data type in a SQL injection UNION attack Having already determined
- 26. Using a SQL injection UNION attack to retrieve interesting data Suppose that: The original query returns
- 27. Retrieving multiple values within a single column For example, on Oracle you could submit the input:
- 28. Examining the database in SQL injection attacks Querying the database type and version Listing the contents
- 29. Querying the database type and version The queries to determine the database version for some popular
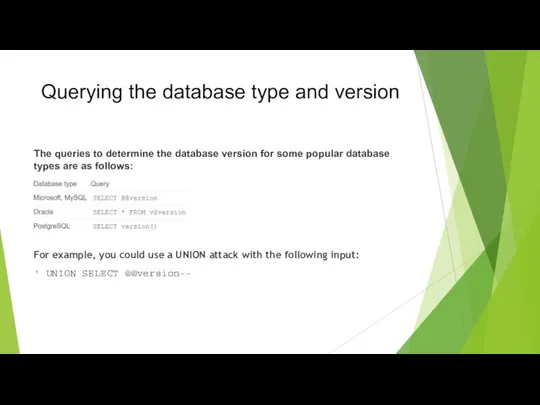
- 30. Listing the contents of the database Most database types (with the notable exception of Oracle) have
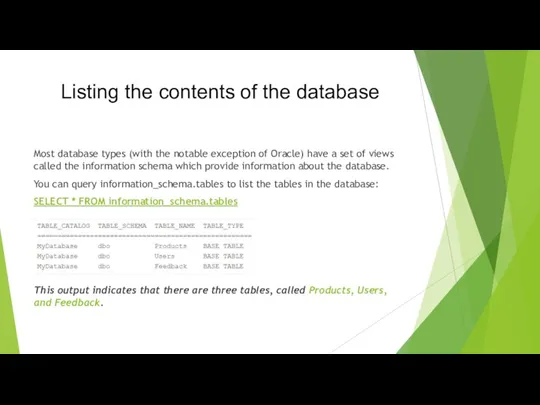
- 31. Listing the contents of the database You can then query information_schema.columns to list the columns in
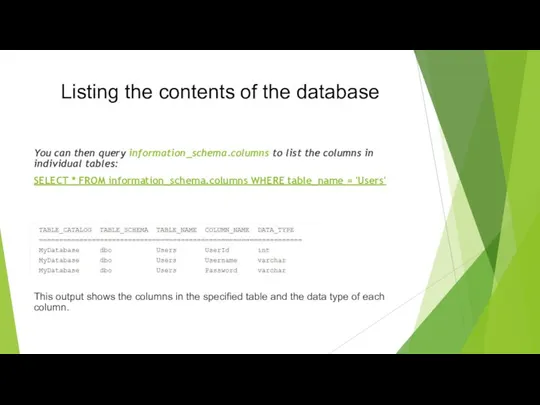
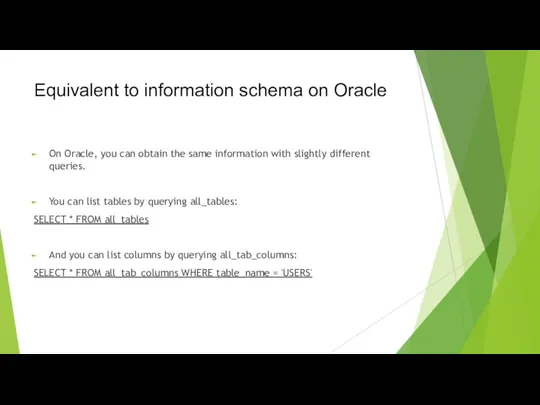
- 32. Equivalent to information schema on Oracle On Oracle, you can obtain the same information with slightly
- 33. How to detect SQL injection vulnerabilities The majority of SQL injection vulnerabilities can be found quickly
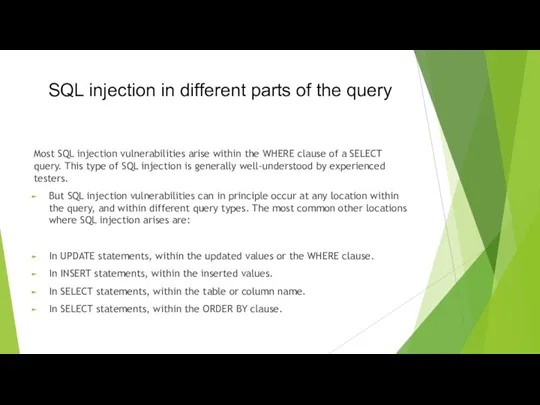
- 34. SQL injection in different parts of the query Most SQL injection vulnerabilities arise within the WHERE
- 35. SQL injection in different contexts In all of the labs so far, you've used the query
- 36. How to prevent SQL injection Most instances of SQL injection can be prevented by using parameterized
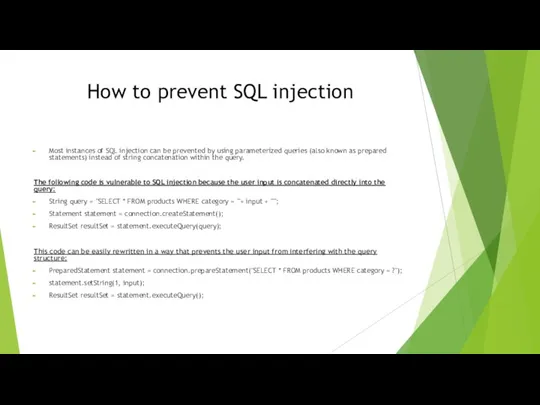
- 37. Second-order SQL injection First-order SQL injection arises where the application takes user input from an HTTP
- 38. Burp Suite's web vulnerability scanner
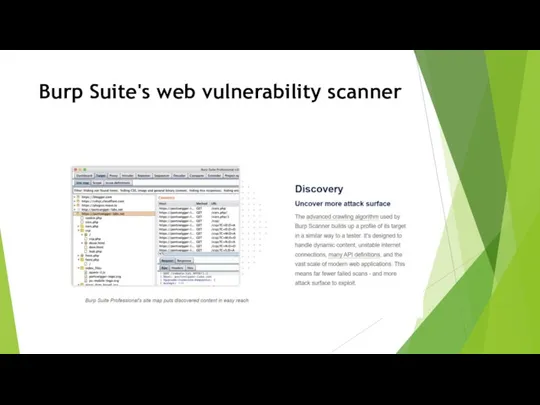
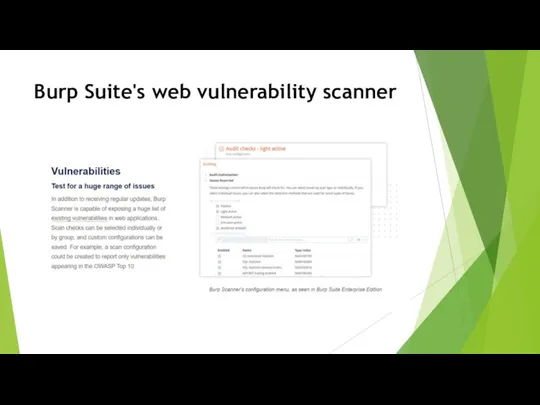
- 39. Burp Suite's web vulnerability scanner The web vulnerability scanner that does more The web vulnerability scanner
- 40. Burp Suite's web vulnerability scanner
- 41. Burp Suite's web vulnerability scanner
- 42. Burp Suite's web vulnerability scanner
- 43. Burp Suite's web vulnerability scanner
- 44. Burp Suite's web vulnerability scanner
- 45. Burp Suite's web vulnerability scanner
- 46. Burp Suite's web vulnerability scanner
- 48. Скачать презентацию









 История информатики
История информатики Настройка сети Windows 7
Настройка сети Windows 7 ELC PBA September 2018
ELC PBA September 2018 Windows Movie Maker
Windows Movie Maker Область видимости и время жизни программы. (Лекция 8)
Область видимости и время жизни программы. (Лекция 8) Архитектура Web-баз данных. Лекция 3.19
Архитектура Web-баз данных. Лекция 3.19 INSTAGRAM – магазин нижнего белья
INSTAGRAM – магазин нижнего белья Операции и стандартные функции Turbo Pascal 7.0
Операции и стандартные функции Turbo Pascal 7.0 Cистема управления версиями Git
Cистема управления версиями Git Эти люди изменили мир
Эти люди изменили мир ГИС Панорама. Разработка программного обеспечения и архитектура геоинформационных систем
ГИС Панорама. Разработка программного обеспечения и архитектура геоинформационных систем Сравнительный анализ дизайна сайтов
Сравнительный анализ дизайна сайтов Самообразование – одна из форм повышения профессионального мастерства педагога
Самообразование – одна из форм повышения профессионального мастерства педагога Отчет по учебной практике ПМ08. Разработка дизайна веб-приложений
Отчет по учебной практике ПМ08. Разработка дизайна веб-приложений Аналіз складних об’єктів і систем. Аналітичні дослідження
Аналіз складних об’єктів і систем. Аналітичні дослідження Multithreading IO Streams Java Core
Multithreading IO Streams Java Core Урок информатики по учебнику Плаксина М.А. темаКак работать с компьютером 3 класс
Урок информатики по учебнику Плаксина М.А. темаКак работать с компьютером 3 класс Возможности программы КОМПАС 3D
Возможности программы КОМПАС 3D Основы боевой подготовки. Лекция №10
Основы боевой подготовки. Лекция №10 Школа подготовки технических администраторов. Домены, хостинги, сайты. (Занятие 11)
Школа подготовки технических администраторов. Домены, хостинги, сайты. (Занятие 11) Presentation template
Presentation template Programming Logic and Design, Seventh Edition
Programming Logic and Design, Seventh Edition Основные понятия объектно-ориентированного языка программирования
Основные понятия объектно-ориентированного языка программирования Первый канал
Первый канал Язык Python в школьном курсе информатики
Язык Python в школьном курсе информатики Решение расчётной задачи в среде электронной таблицы EXCEL
Решение расчётной задачи в среде электронной таблицы EXCEL Маркировка. Поддержка в 1С. Практика автоматизации с пользой для бизнеса
Маркировка. Поддержка в 1С. Практика автоматизации с пользой для бизнеса Моделирование 9 класс
Моделирование 9 класс