Содержание
- 2. Cyber Preparedness
- 3. Cyber Preparedness
- 4. Technology? Security team? Processes? Where Does Cyber Preparedness Begin?
- 5. It starts with The Board. It is driven by a culture where cyber risk is addressed
- 6. Why Should They Care?
- 7. The Obvious
- 8. Reducing Risk. Enables Growth.
- 9. Cyber Preparedness
- 10. Fire started in a NJ home last year A driver saw the fire and banged on
- 11. Effective Smoke Detection Consider where you replace them Ensure the batteries work Monitor and maintain
- 12. Have a Plan for When the Alarm Goes Off Think of this as Incident Response The
- 13. What if there’s a “fire” in your network? What if the alarms don’t go off right
- 14. Hierarchy of Security Needs To be fully prepared and avoid disasters: Detect new, hidden threats Effectively
- 15. Prevention: Still Important
- 16. Balancing Spend Allocations Prevention Detection Response
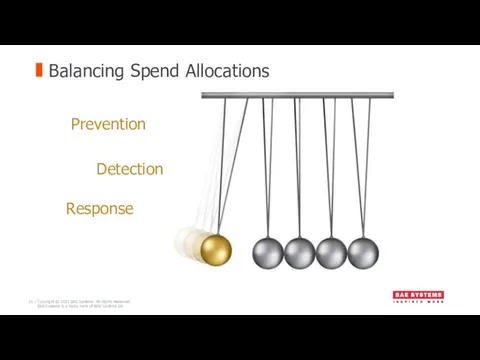
- 17. detect the incident. The ability to respond to an incident is only as good as an
- 18. Detection Too many bad guys/attacks Bad guys don’t want to be found Attacks take new forms
- 19. Analytics Techniques Attacks Detection Techniques Anomaly Detection Analytics Unsupervised machine learning Anomaly Detection Analytics Behavioural Analytics
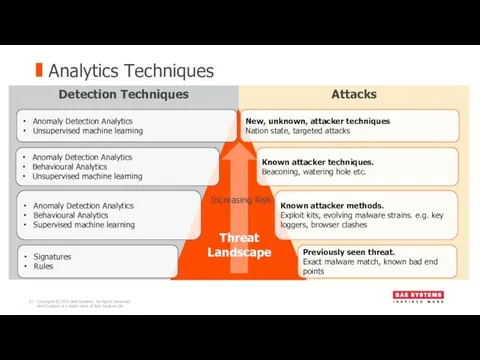
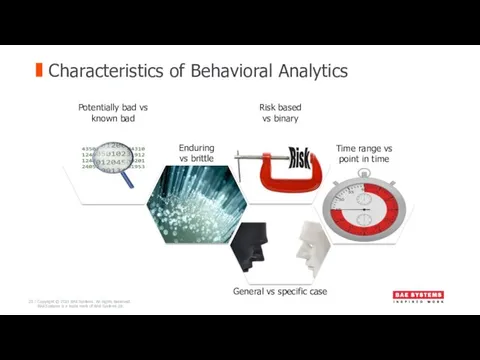
- 20. Characteristics of Behavioral Analytics
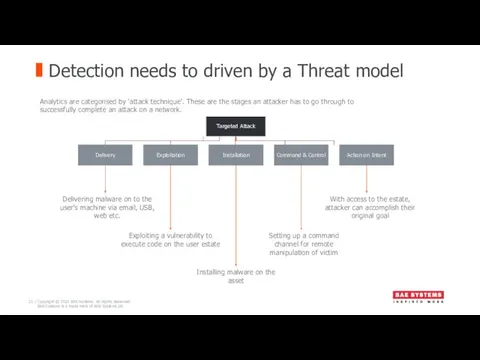
- 21. Detection needs to driven by a Threat model Delivering malware on to the user’s machine via
- 22. Cyber Preparedness
- 23. Response
- 24. Having proper analysis capabilities requires both trained personnel and the proper tools to perform the analysis.
- 25. A PLAN vs A FRAMEWORK "No plan of operations extends with certainty beyond the first encounter
- 26. FRAMEWORK Authority and Scope Team Members and Responsibilities Logistics Process to determine severity and escalation Post-Incident
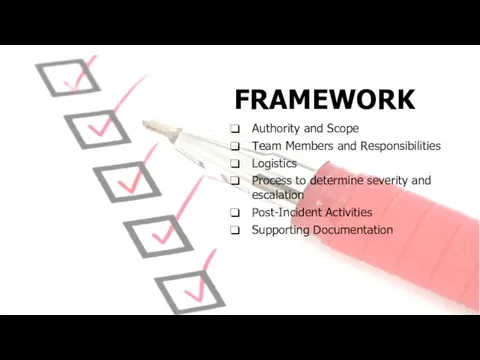
- 27. The most critical component in any Incident Response Practice … Authority and backing from executive management.
- 28. IR Team Primary team Extended team Third parties
- 29. Primary Security Team IR Lead Operations Team Service Desk Team
- 30. Extended Executives Legal Communications Human Resources Compliance Physical Security
- 31. 3rd Parties Outsourced IT (help desk, server support) Forensic Firms ISPs Legal Counsel Law Enforcement Public
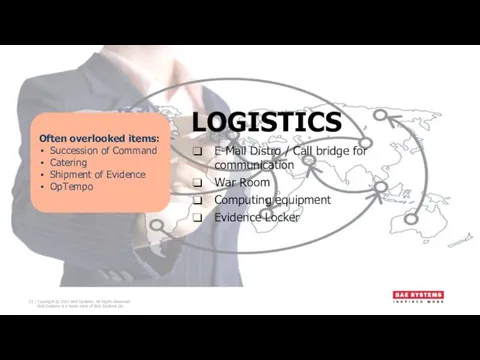
- 32. LOGISTICS E-Mail Distro / Call bridge for communication War Room Computing equipment Evidence Locker Often overlooked
- 33. Testing Incident Response High Level Audit Objective Based Assessment Table top Exercise War Game
- 34. Cyber Preparedness – Key Takeaways
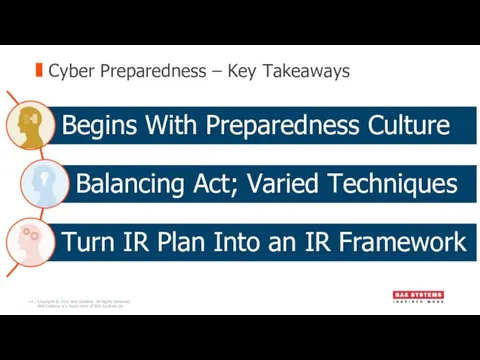
- 35. Thank You
- 36. Q&A
- 37. BAE Systems Surrey Research Park Guildford Surrey GU2 7YP United Kingdom T: +44 (0)1483 816000 F:
- 39. Скачать презентацию









 Конспект образовательной деятельности по экологии в средней группе с использованием ИКТ на тему: Берегите лес
Конспект образовательной деятельности по экологии в средней группе с использованием ИКТ на тему: Берегите лес Основные характеристики центрального процессора
Основные характеристики центрального процессора методическое пособие
методическое пособие Теоретические основы органической химии
Теоретические основы органической химии немного обо мне
немного обо мне Автоматизация звука Ч в словах, предложениях.
Автоматизация звука Ч в словах, предложениях. Презентация Панорама классного часа.
Презентация Панорама классного часа. Перинатальная патология центральной нервной системы
Перинатальная патология центральной нервной системы Синегнойная палочка (Pseudomonas aeruginosa)
Синегнойная палочка (Pseudomonas aeruginosa) Навигационное планирование и подготовка судна к переходу по маршруту
Навигационное планирование и подготовка судна к переходу по маршруту Балалар ертегілері
Балалар ертегілері Моя будущая профессия: Стоматолог
Моя будущая профессия: Стоматолог Представление о семье!!!
Представление о семье!!! Базовые понятия языка Си
Базовые понятия языка Си Знаменитые люди поселка Вырица. Иван Антонович Ефремов
Знаменитые люди поселка Вырица. Иван Антонович Ефремов Презентация 1
Презентация 1 Шероховатость поверхности
Шероховатость поверхности Система финансирования дополнительных занятий
Система финансирования дополнительных занятий Любимый мой Башкортостан
Любимый мой Башкортостан проект Солнышко в технике изонити
проект Солнышко в технике изонити Моя мама учитель. презентация
Моя мама учитель. презентация Физиология нейрона, нервного волокна и синапса
Физиология нейрона, нервного волокна и синапса Кроссворд на тему Отечественная война 1812 года
Кроссворд на тему Отечественная война 1812 года класс. ЛР №5
класс. ЛР №5 Конденсационная установка
Конденсационная установка Презентация Весёлая гимнастика для язычка часть2
Презентация Весёлая гимнастика для язычка часть2 XIX Всемирный фестиваль молодёжи и студентов
XIX Всемирный фестиваль молодёжи и студентов Сегментирование и позиционирование
Сегментирование и позиционирование