Слайд 2
SNORT IDS
Бесплатная система обнаружения
атак с открытым исходным кодом
(free open
source IDS)
Разработчик — Мартин Рош
(developed by Martin Roesch)
Существуют готовые версии для ОС
(binary versions exist for):
OpenSuSE, OpenBSD, FreeBSD, CentOS,
Ubuntu, Windows, etc.
Сетевая СОА (network-based IDS)
Слайд 3
ОСНОВНЫЕ КОМПОНЕНТЫ
(COMPONENTS)
Декодер пакетов (packet decoder)
Проверяет данные на соответствие заявленному протоколу
(checks
if data match declared protocol)
Препроцессоры (preprocessors)
Подключаемые модули, позволяющие СОА
проводить более детальный анализ пакетов (plug-in modules that allow more detailed
packet analysis)
Слайд 4
ОСНОВНЫЕ КОМПОНЕНТЫ
(COMPONENTS)
Модуль обнаружения (detection engine)
Основной компонент СОА, отвечающий
за обнаружение атак.
Сопоставляет сетевой трафик с набором правил.
Basic IDS component than is responsible for attack detection. Checks network traffic against
the set of rules.
Слайд 5
ОСНОВНЫЕ КОМПОНЕНТЫ
(COMPONENTS)
Модуль вывода (output module)
Управляет выводом информации об обнаруженных атаках в
файлы и базы данных
Records information about detected attacks to files and databases
Слайд 6
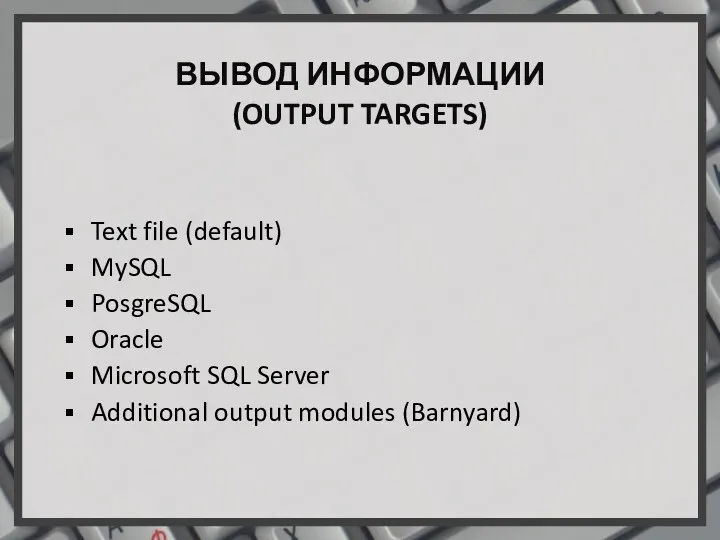
ВЫВОД ИНФОРМАЦИИ
(OUTPUT TARGETS)
Text file (default)
MySQL
PosgreSQL
Oracle
Microsoft SQL Server
Additional output modules (Barnyard)
Слайд 7
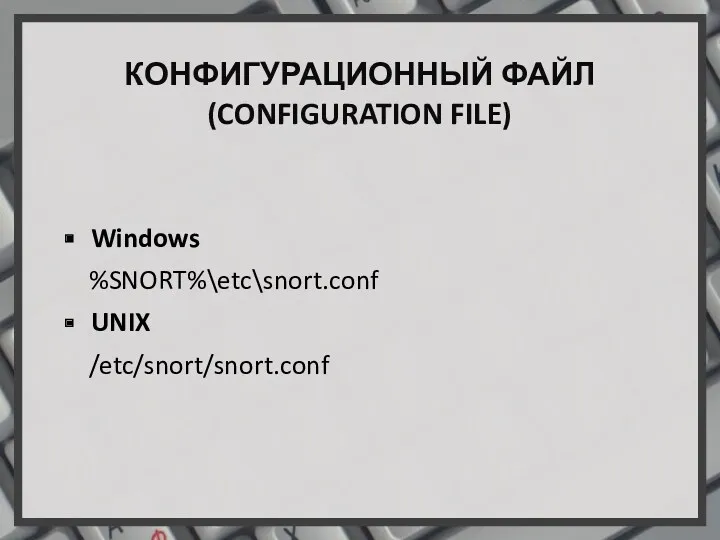
КОНФИГУРАЦИОННЫЙ ФАЙЛ
(CONFIGURATION FILE)
Windows
%SNORT%\etc\snort.conf
UNIX
/etc/snort/snort.conf
Слайд 8
![ПЕРЕМЕННЫЕ (VARIABLES) var var RULES_PATH c:\snort\rules portvar portvar MY_PORTS [22,80,1024:1050]](/_ipx/f_webp&q_80&fit_contain&s_1440x1080/imagesDir/jpg/589450/slide-7.jpg)
ПЕРЕМЕННЫЕ
(VARIABLES)
var
var RULES_PATH c:\snort\rules
portvar
portvar MY_PORTS [22,80,1024:1050]
ipvar
ipvar HOME_NET 192.168.1.0/24
ipvar EXTERNAL_NET any
Слайд 9
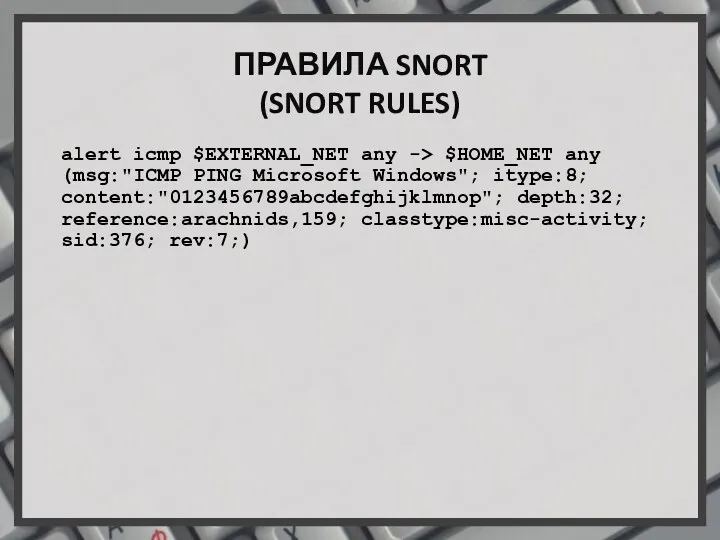
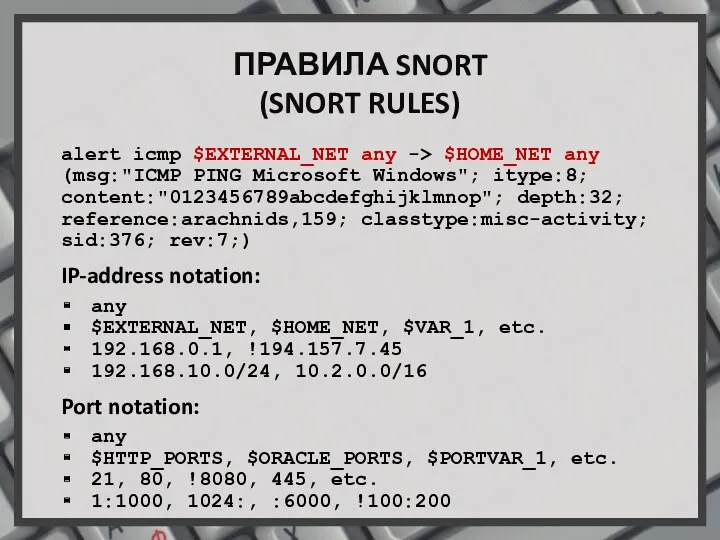
ПРАВИЛА SNORT
(SNORT RULES)
alert icmp $EXTERNAL_NET any -> $HOME_NET any (msg:"ICMP PING
Microsoft Windows"; itype:8; content:"0123456789abcdefghijklmnop"; depth:32; reference:arachnids,159; classtype:misc-activity; sid:376; rev:7;)
Слайд 10
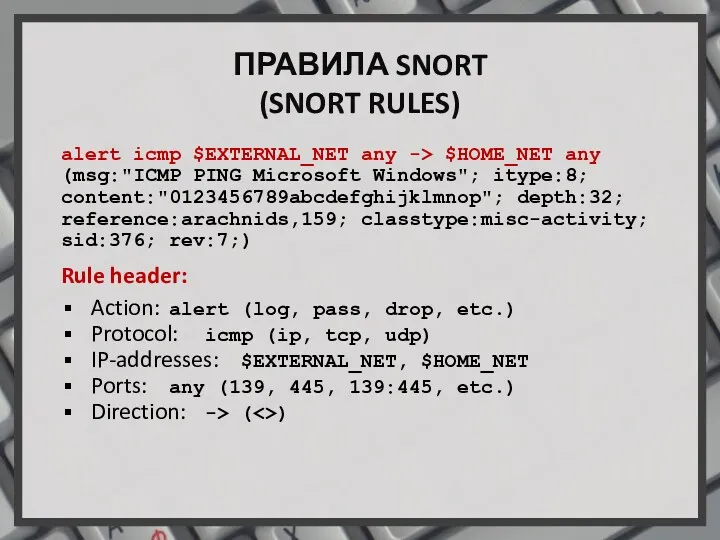
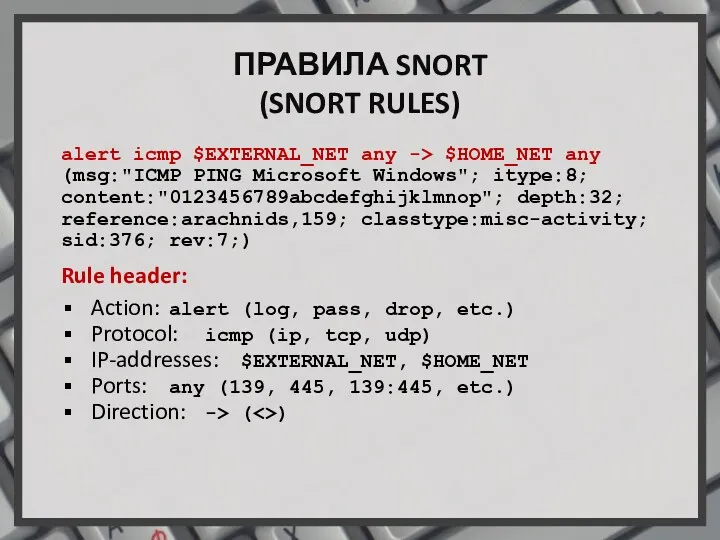
ПРАВИЛА SNORT
(SNORT RULES)
alert icmp $EXTERNAL_NET any -> $HOME_NET any (msg:"ICMP PING
Microsoft Windows"; itype:8; content:"0123456789abcdefghijklmnop"; depth:32; reference:arachnids,159; classtype:misc-activity; sid:376; rev:7;)
Rule header:
Action: alert (log, pass, drop, etc.)
Protocol: icmp (ip, tcp, udp)
IP-addresses: $EXTERNAL_NET, $HOME_NET
Ports: any (139, 445, 139:445, etc.)
Direction: -> (<>)
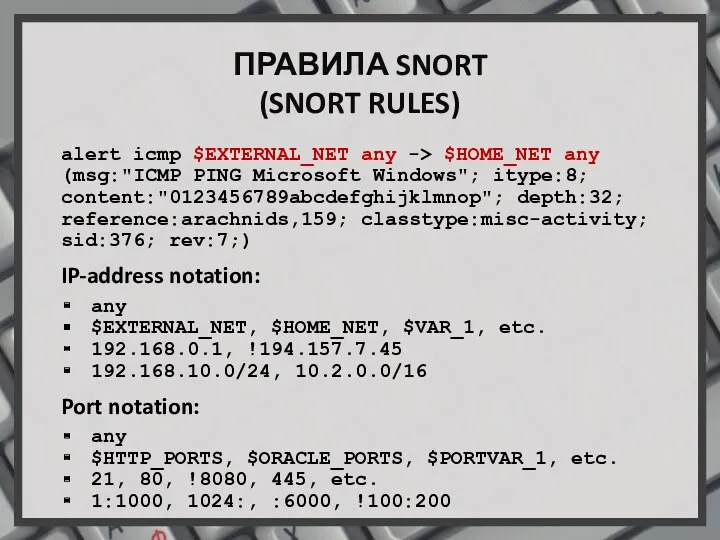
Слайд 11
ПРАВИЛА SNORT
(SNORT RULES)
alert icmp $EXTERNAL_NET any -> $HOME_NET any (msg:"ICMP PING
Microsoft Windows"; itype:8; content:"0123456789abcdefghijklmnop"; depth:32; reference:arachnids,159; classtype:misc-activity; sid:376; rev:7;)
IP-address notation:
any
$EXTERNAL_NET, $HOME_NET, $VAR_1, etc.
192.168.0.1, !194.157.7.45
192.168.10.0/24, 10.2.0.0/16
Port notation:
any
$HTTP_PORTS, $ORACLE_PORTS, $PORTVAR_1, etc.
21, 80, !8080, 445, etc.
1:1000, 1024:, :6000, !100:200
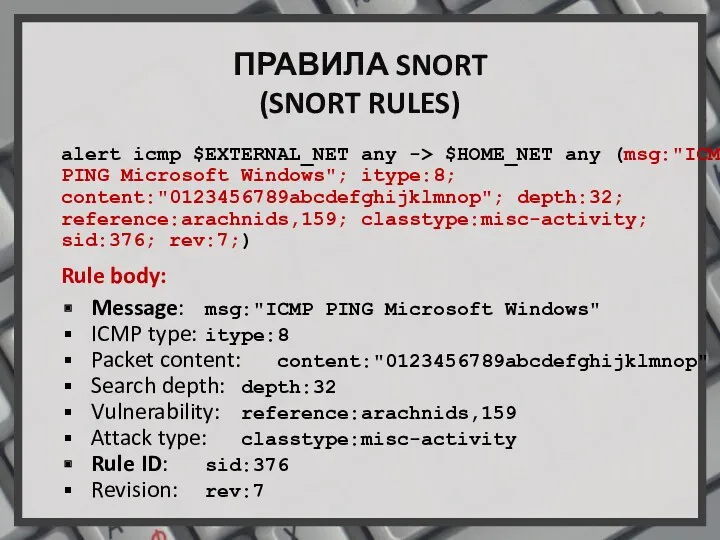
Слайд 12
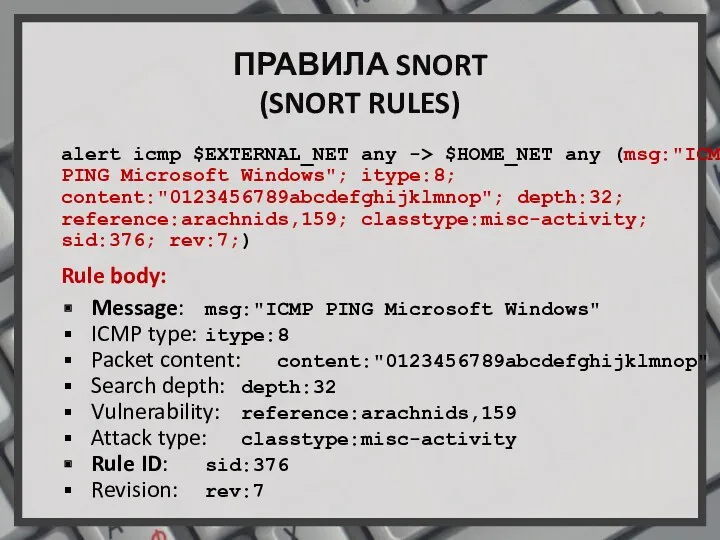
ПРАВИЛА SNORT
(SNORT RULES)
alert icmp $EXTERNAL_NET any -> $HOME_NET any (msg:"ICMP PING
Microsoft Windows"; itype:8; content:"0123456789abcdefghijklmnop"; depth:32; reference:arachnids,159; classtype:misc-activity; sid:376; rev:7;)
Rule body:
Message: msg:"ICMP PING Microsoft Windows"
ICMP type: itype:8
Packet content: content:"0123456789abcdefghijklmnop"
Search depth: depth:32
Vulnerability: reference:arachnids,159
Attack type: classtype:misc-activity
Rule ID: sid:376
Revision: rev:7
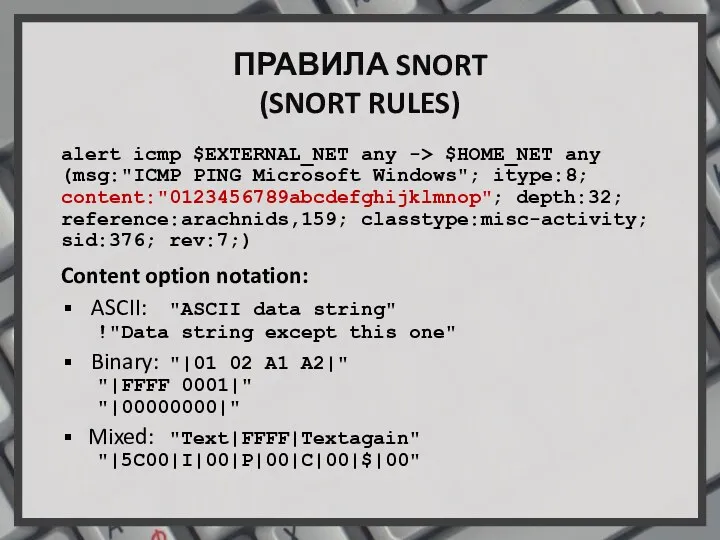
Слайд 13
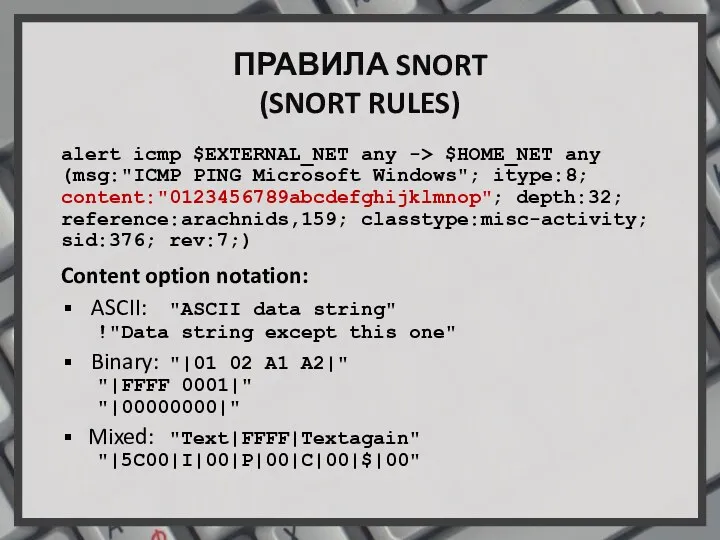
ПРАВИЛА SNORT
(SNORT RULES)
alert icmp $EXTERNAL_NET any -> $HOME_NET any (msg:"ICMP PING
Microsoft Windows"; itype:8; content:"0123456789abcdefghijklmnop"; depth:32; reference:arachnids,159; classtype:misc-activity; sid:376; rev:7;)
Content option notation:
ASCII: "ASCII data string"
!"Data string except this one"
Binary: "|01 02 A1 A2|"
"|FFFF 0001|"
"|00000000|"
Mixed: "Text|FFFF|Textagain"
"|5C00|I|00|P|00|C|00|$|00"
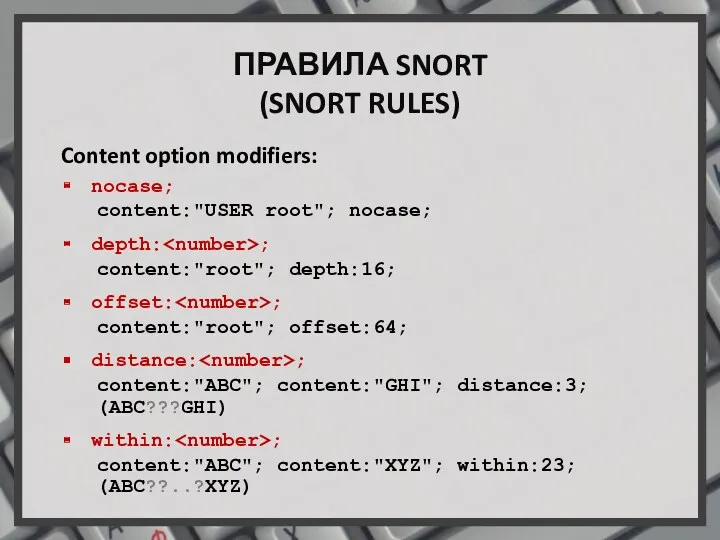
Слайд 14
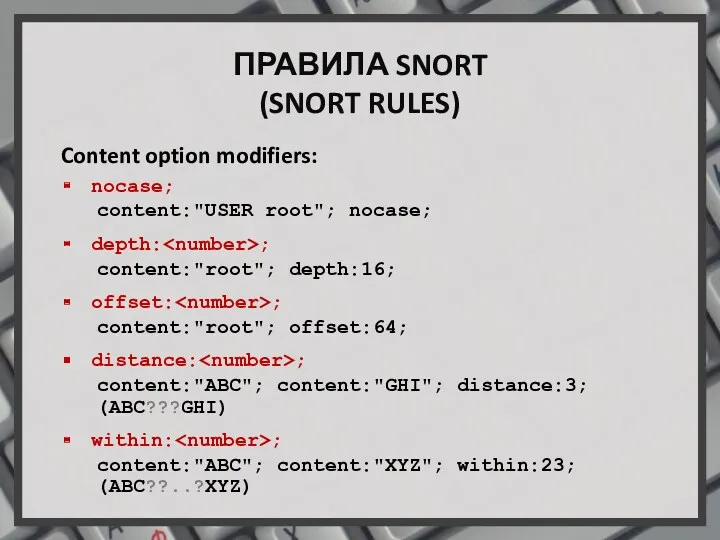
ПРАВИЛА SNORT
(SNORT RULES)
Content option modifiers:
nocase;
content:"USER root"; nocase;
depth:;
content:"root"; depth:16;
offset:;
content:"root"; offset:64;
distance:;
content:"ABC"; content:"GHI"; distance:3;
(ABC???GHI)
within:;
content:"ABC";
content:"XYZ"; within:23;
(ABC??..?XYZ)
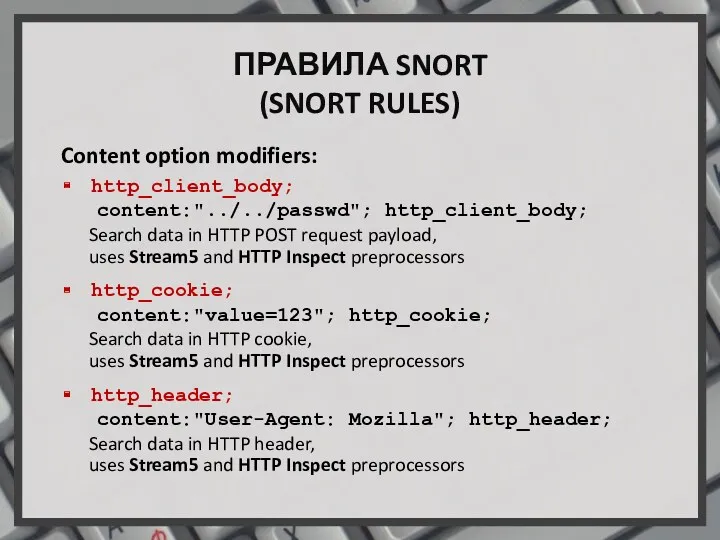
Слайд 15
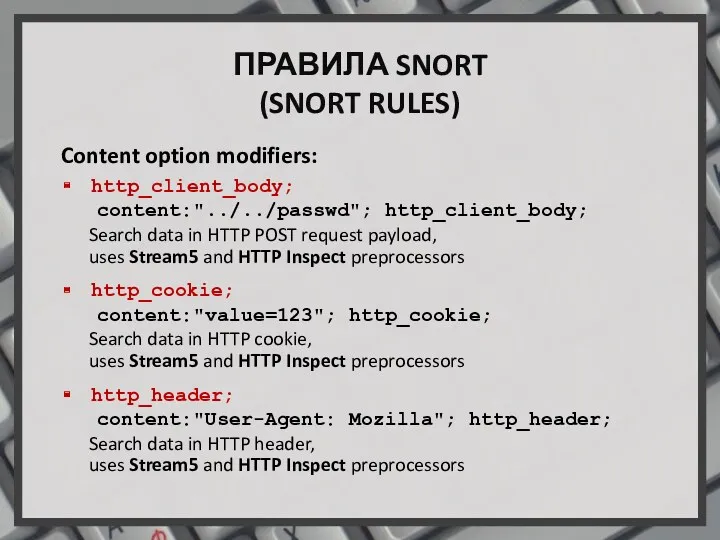
ПРАВИЛА SNORT
(SNORT RULES)
Content option modifiers:
http_client_body;
content:"../../passwd"; http_client_body;
Search data in HTTP POST request
payload,
uses Stream5 and HTTP Inspect preprocessors
http_cookie;
content:"value=123"; http_cookie;
Search data in HTTP cookie,
uses Stream5 and HTTP Inspect preprocessors
http_header;
content:"User-Agent: Mozilla"; http_header;
Search data in HTTP header,
uses Stream5 and HTTP Inspect preprocessors
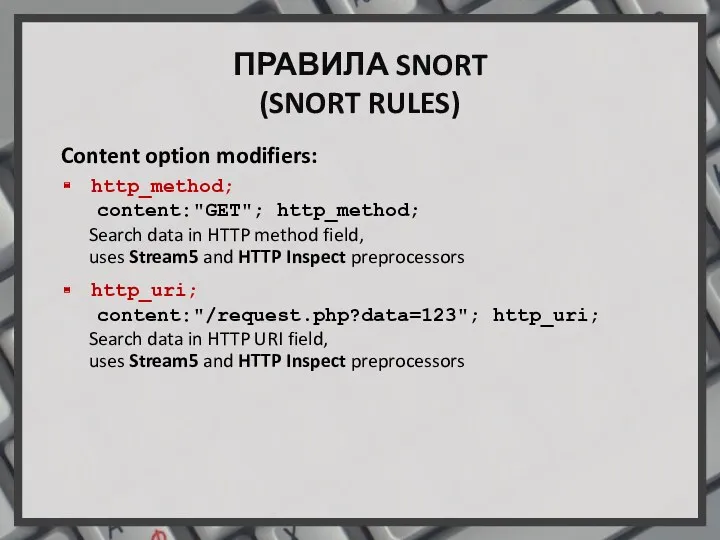
Слайд 16
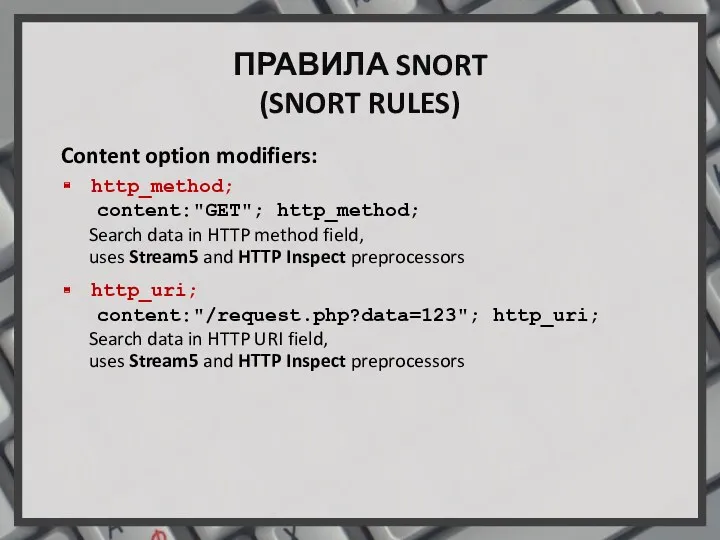
ПРАВИЛА SNORT
(SNORT RULES)
Content option modifiers:
http_method;
content:"GET"; http_method;
Search data in HTTP method field,
uses Stream5 and HTTP Inspect preprocessors
http_uri;
content:"/request.php?data=123"; http_uri;
Search data in HTTP URI field,
uses Stream5 and HTTP Inspect preprocessors
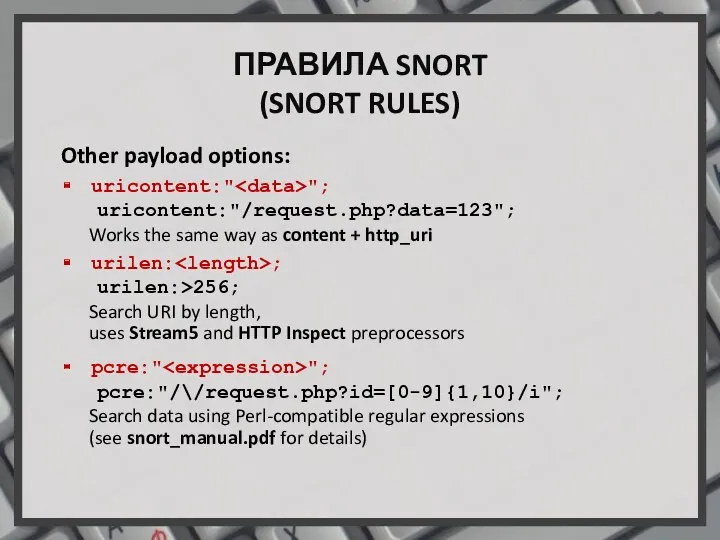
Слайд 17
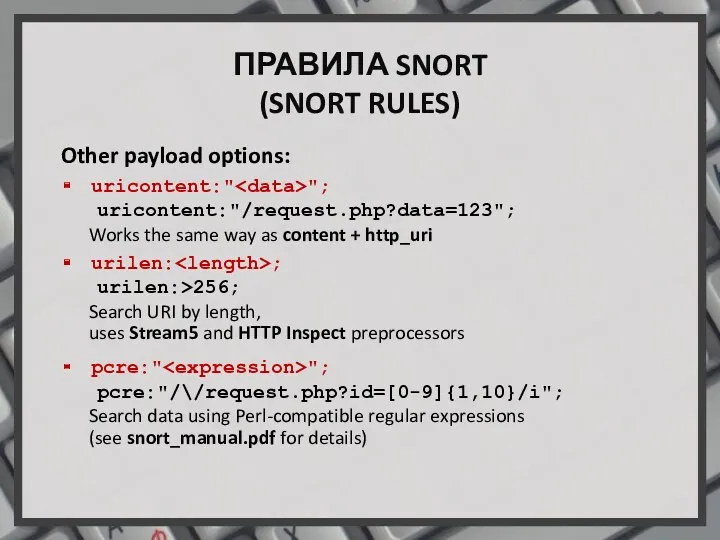
ПРАВИЛА SNORT
(SNORT RULES)
Other payload options:
uricontent:"";
uricontent:"/request.php?data=123";
Works the same way as content +
http_uri
urilen:;
urilen:>256;
Search URI by length,
uses Stream5 and HTTP Inspect preprocessors
pcre:"";
pcre:"/\/request.php?id=[0-9]{1,10}/i";
Search data using Perl-compatible regular expressions
(see snort_manual.pdf for details)
Слайд 18
![ПРАВИЛА SNORT (SNORT RULES) Non-payload options: flags:[!|*|+] [, ]; flags:*AR;](/_ipx/f_webp&q_80&fit_contain&s_1440x1080/imagesDir/jpg/589450/slide-17.jpg)
ПРАВИЛА SNORT
(SNORT RULES)
Non-payload options:
flags:[!|*|+][,];
flags:*AR;
ACK+RST+…
flow:[(established|stateless)]
[,(to_client|to_server|from_client|from_server)]
[,(no_stream|only_stream)];
flow:established,from_server;
Search for packets transmitted from server to client
within
the TCP connection, uses Stream5 preprocessor
Слайд 19
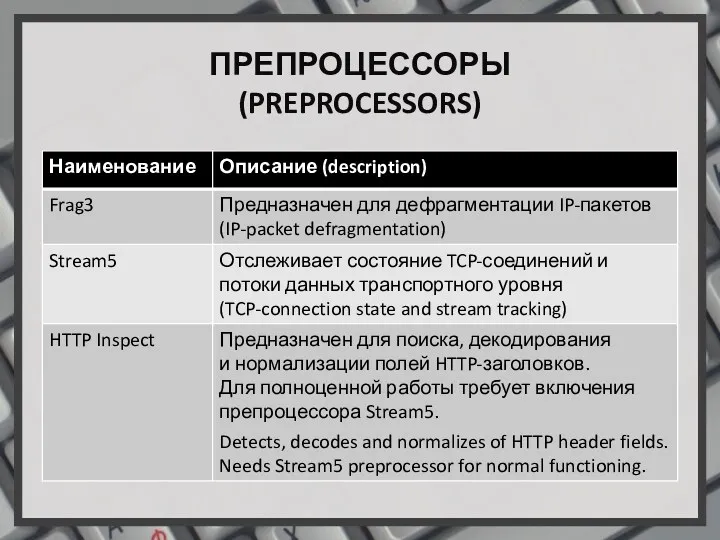
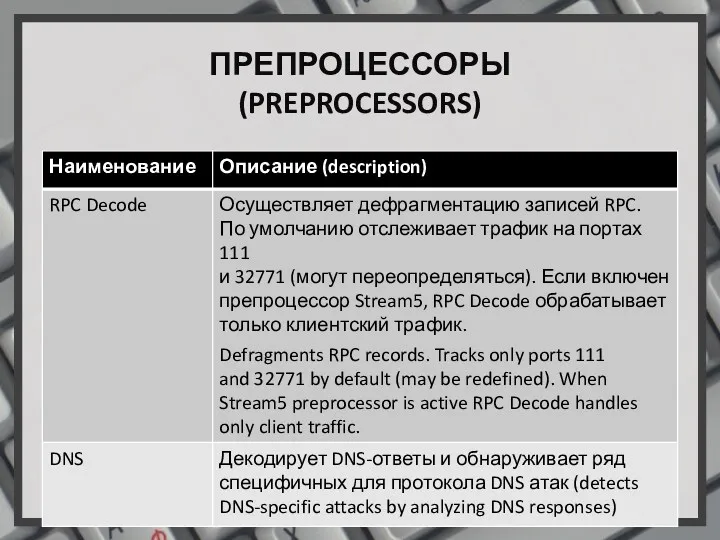
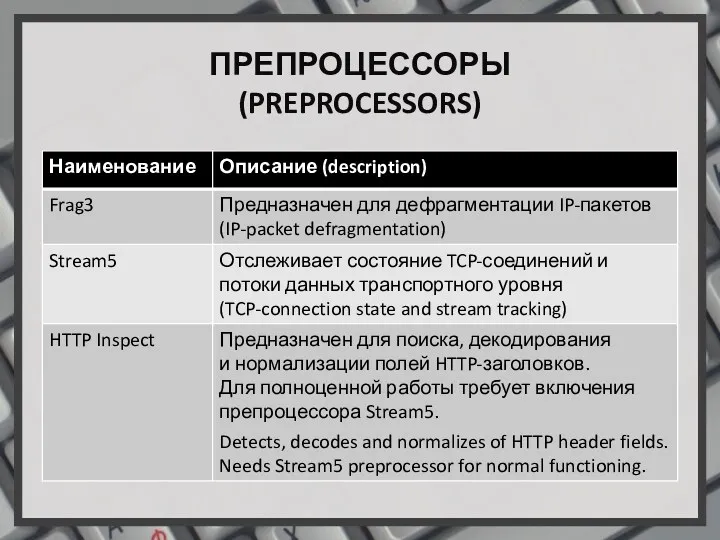
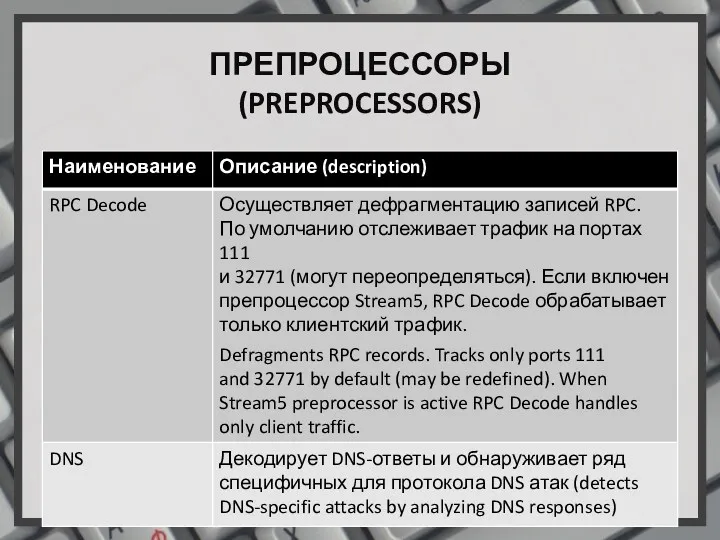
ПРЕПРОЦЕССОРЫ
(PREPROCESSORS)
Слайд 20
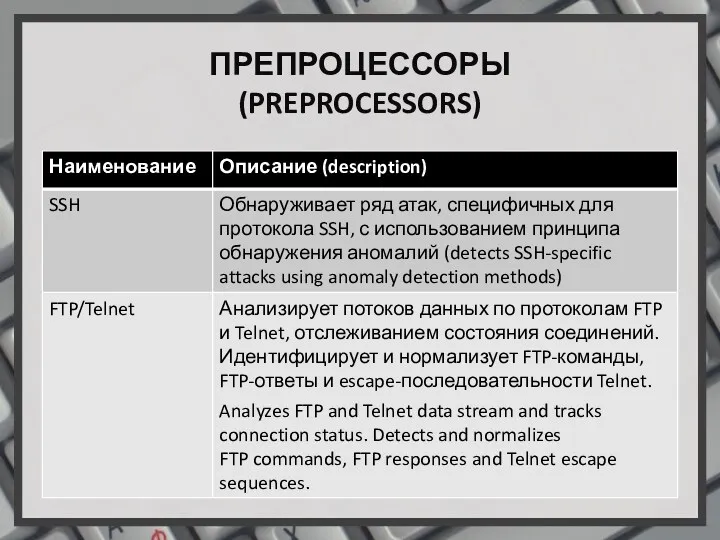
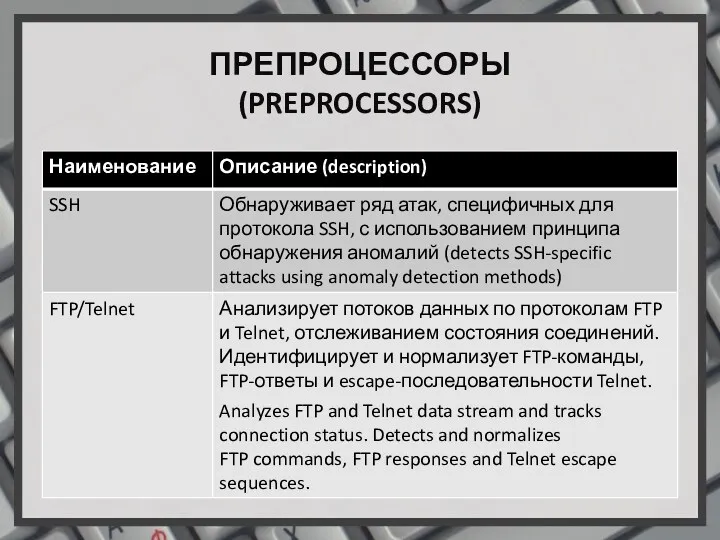
ПРЕПРОЦЕССОРЫ
(PREPROCESSORS)
Слайд 21
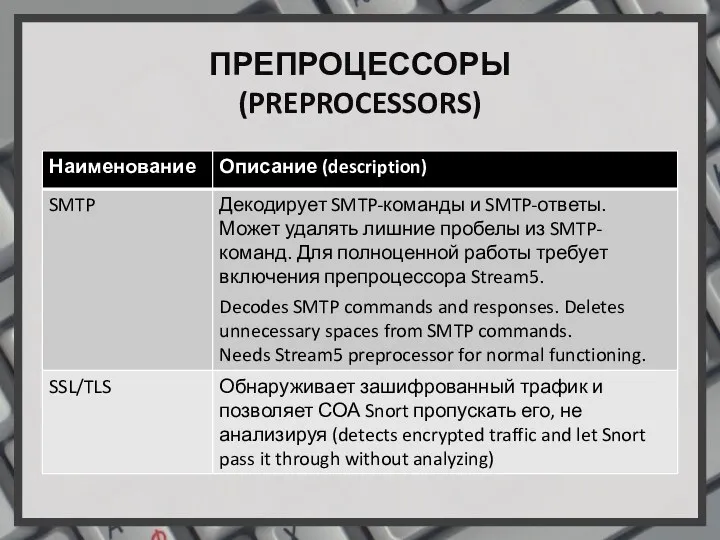
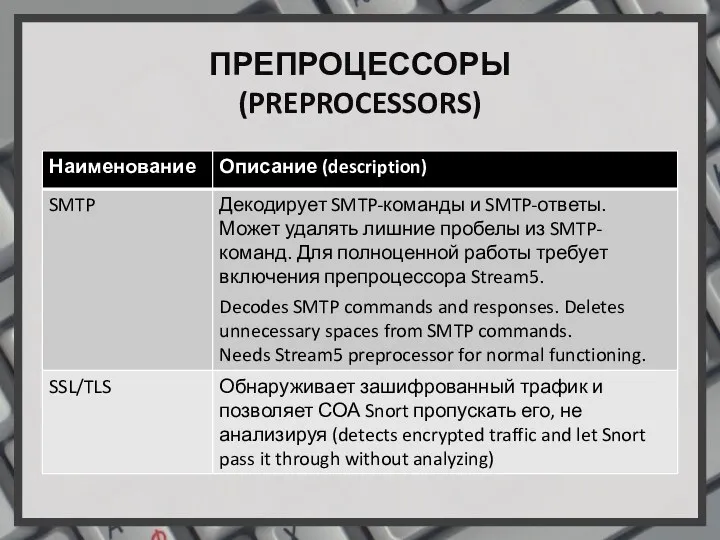
ПРЕПРОЦЕССОРЫ
(PREPROCESSORS)
Слайд 22
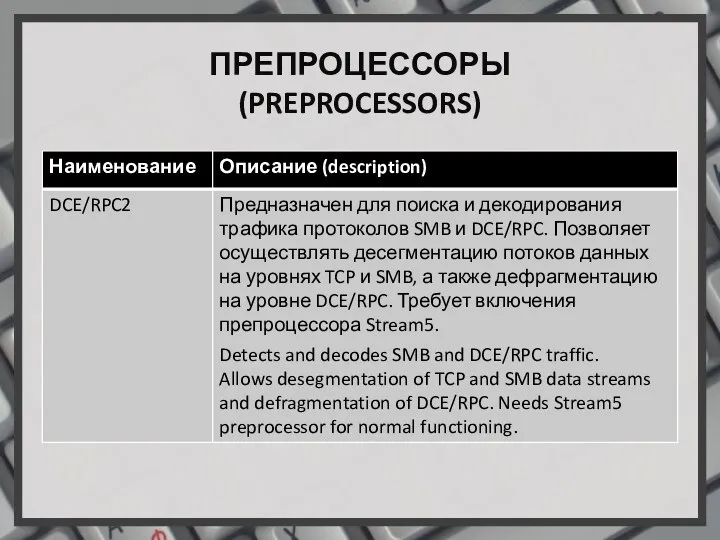
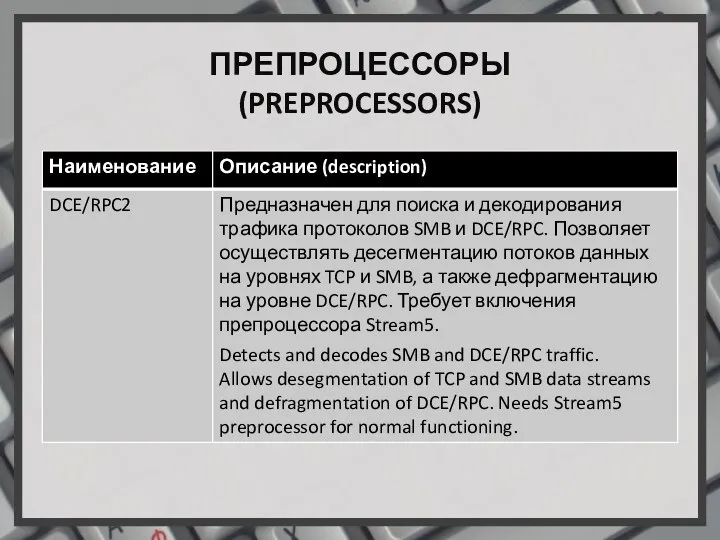
ПРЕПРОЦЕССОРЫ
(PREPROCESSORS)
Слайд 23
ПРЕПРОЦЕССОРЫ
(PREPROCESSORS)
![ПЕРЕМЕННЫЕ (VARIABLES) var var RULES_PATH c:\snort\rules portvar portvar MY_PORTS [22,80,1024:1050]](/_ipx/f_webp&q_80&fit_contain&s_1440x1080/imagesDir/jpg/589450/slide-7.jpg)
![ПРАВИЛА SNORT (SNORT RULES) Non-payload options: flags:[!|*|+] [, ]; flags:*AR;](/_ipx/f_webp&q_80&fit_contain&s_1440x1080/imagesDir/jpg/589450/slide-17.jpg)
 Гайд по настройке и использованию SSH - Secure Shell, сетевой протокол
Гайд по настройке и использованию SSH - Secure Shell, сетевой протокол Создание веб приложения Music Manager
Создание веб приложения Music Manager Компьютерные технологии на службе криминалистики
Компьютерные технологии на службе криминалистики Базовое Администрирование Linux
Базовое Администрирование Linux Збереження інформації
Збереження інформації Обобщенная линейная модель множественной регрессии с гетероскедастичными остатками. Лекция 8
Обобщенная линейная модель множественной регрессии с гетероскедастичными остатками. Лекция 8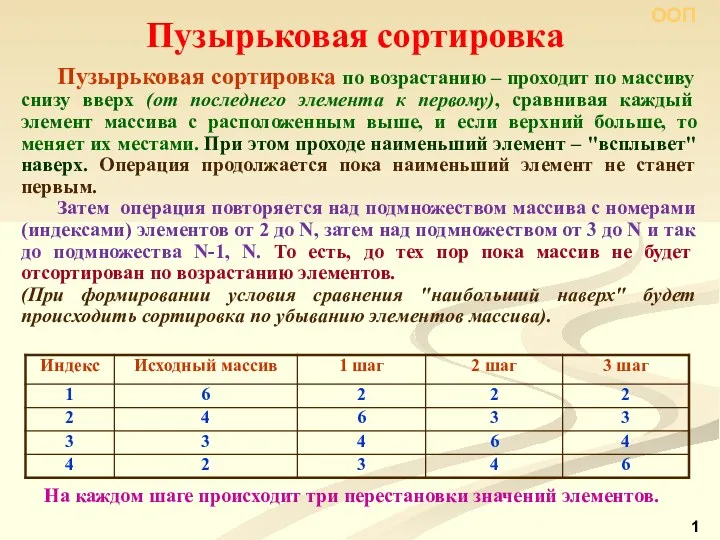 Пузырьковая сортировка
Пузырьковая сортировка Облачные технологии
Облачные технологии Четыре основных принципа объектно-ориентированного программирования
Четыре основных принципа объектно-ориентированного программирования Персональные компьютеры
Персональные компьютеры Методы сортировки и поиска
Методы сортировки и поиска Процедурные расширения SQL. Хранимые процедуры и триггеры
Процедурные расширения SQL. Хранимые процедуры и триггеры Классификация программных продуктов
Классификация программных продуктов Welcome. Anti-virus
Welcome. Anti-virus Антивирусные программы
Антивирусные программы Сеть Ethernet. Построение коммутируемой сети
Сеть Ethernet. Построение коммутируемой сети Кейс сервисов Веб 2.0
Кейс сервисов Веб 2.0 Структура сайта школьного музея
Структура сайта школьного музея Передача информации.
Передача информации. Практическое применение 3D-моделирования
Практическое применение 3D-моделирования Справочно-библиографический аппарат Колмовской библиотеки, Великий Новгород
Справочно-библиографический аппарат Колмовской библиотеки, Великий Новгород Анализ данных в реляционных БД на примере СУБД MS Access. Создание запросов, изменяющих таблицы. Создание отчетов
Анализ данных в реляционных БД на примере СУБД MS Access. Создание запросов, изменяющих таблицы. Создание отчетов Команди для малювання в середовищі Scratch
Команди для малювання в середовищі Scratch Устройство компьютера
Устройство компьютера Безопасность систем баз данных. Обеспечение целостности
Безопасность систем баз данных. Обеспечение целостности Расширенный алгоритм Евклида. Разбор задач
Расширенный алгоритм Евклида. Разбор задач Программирование на языке C++
Программирование на языке C++ Информационная система Недра
Информационная система Недра