Содержание
- 2. Overview Discussion of the “Same Origin Policy” Overview of the “Sleeping Giant” The Introduction of 2
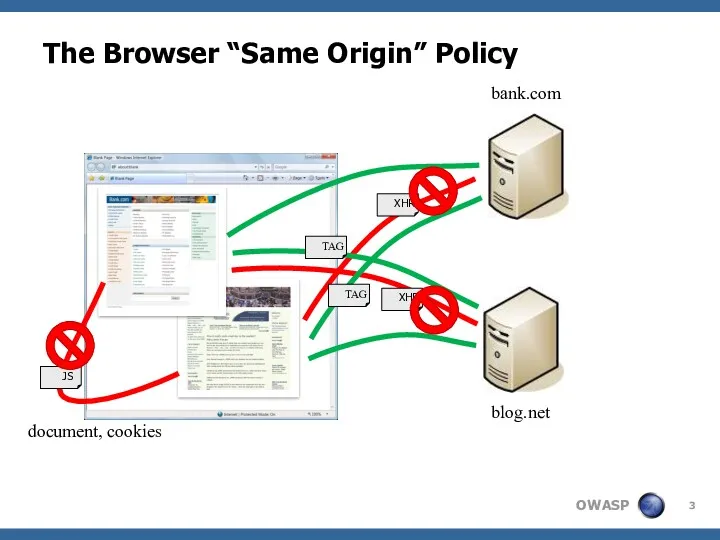
- 3. The Browser “Same Origin” Policy bank.com blog.net XHR XHR document, cookies TAG TAG JS
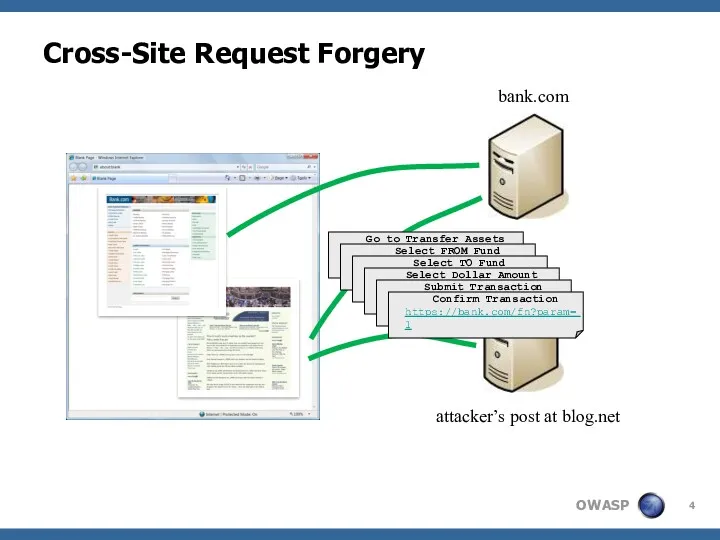
- 4. Cross-Site Request Forgery bank.com attacker’s post at blog.net Go to Transfer Assets https://bank.com/fn?param=1 Select FROM Fund
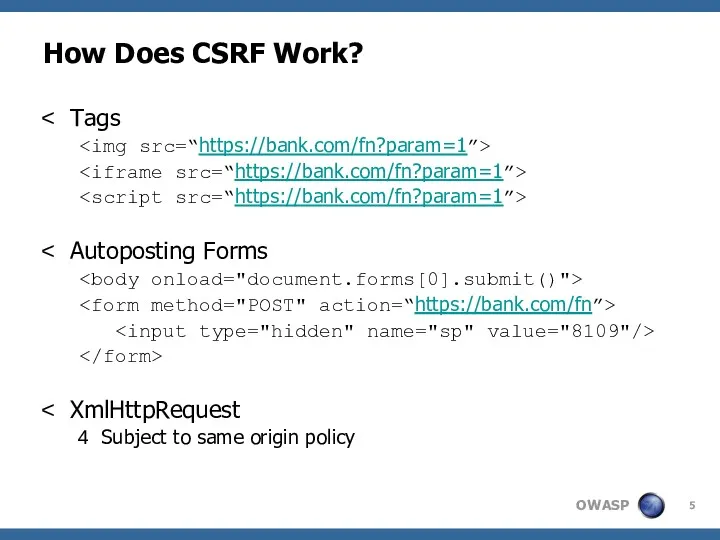
- 5. How Does CSRF Work? Tags Autoposting Forms XmlHttpRequest Subject to same origin policy
- 6. Credentials Included bank.com blog.net https://bank.com/fn?param=1 JSESSIONID=AC934234…
- 7. New Tool: OWASP CSRFTester Test your applications for CSRF Record and replay transactions Tune the recorded
- 8. DEMO: OWASP CSRFTester
- 9. What Can Attackers Do with CSRF? Anything an authenticated user can do Click links Fill out
- 10. Using CSRF to Attack Internal Pages attacker.com internal.mybank.com Allowed! CSRF Internal Site TAG internal browser
- 11. Misconceptions – Defenses That Don’t Work Only accept POST Stops simple link-based attacks (IMG, frames, etc.)
- 12. New Tool: OWASP CSRFGuard 2.0 User (Browser) 1. Add token with regex 2. Add token with
- 13. DEMO: OWASP CSRFGuard 2.0
- 14. Similar Implementations PHP CSRFGuard PHP Implementation of CSRFGuard http://www.owasp.org/index.php/PHP_CSRF_Guard JSCK PHP & JavaScript implementation http://www.thespanner.co.uk/2007/10/19/jsck/
- 15. DEMO: Cross-Site Scripting vs. CSRFGuard
- 16. Enterprise CSRF Mitigation Strategy Balance Between Security, Usability, and Cost MISSION CRITICAL FUNCTIONS EVERYDAY BUSINESS FUNCTIONS
- 17. http://www.owasp.org/index.php/Cross-Site_Request_Forgery http://www.cgisecurity.com/articles/csrf-faq.shtml http://www.darkreading.com/document.asp?doc_id=107651&WT.svl=news1_2
- 18. Extra: How Widespread Are CSRF Holes? Very likely in most web applications Including both intranet and
- 19. Extra: Real World CSRF Examples
- 21. Скачать презентацию
 Алгоритм и его свойства. Формы записи алгоритмов
Алгоритм и его свойства. Формы записи алгоритмов Хакерские улиты и защита от них
Хакерские улиты и защита от них Виды внеклассной работы по информатике
Виды внеклассной работы по информатике Програмне забезпечення для графічної візуалізації даних на платформі Android
Програмне забезпечення для графічної візуалізації даних на платформі Android ОС вопросы1_12
ОС вопросы1_12 Объекты ядра Windows
Объекты ядра Windows Виды информации
Виды информации Компьютер - мой помощник
Компьютер - мой помощник Microsoft Word 2010
Microsoft Word 2010 Глобальные компьютерные сети
Глобальные компьютерные сети Файловая система. Функции ОС по управлению файлами
Файловая система. Функции ОС по управлению файлами Тезаурус Безопасный интернет
Тезаурус Безопасный интернет Игра по информатике Защита информации
Игра по информатике Защита информации Растровые и векторные изображения
Растровые и векторные изображения Технологии создания мультимедийной платформы. Мультимедийная журналистика
Технологии создания мультимедийной платформы. Мультимедийная журналистика Методическая разработка по информатике и ИКТ на тему Форматирование абзацев и стили форматирования в Microsoft Office Word
Методическая разработка по информатике и ИКТ на тему Форматирование абзацев и стили форматирования в Microsoft Office Word Основные изменения в ПО
Основные изменения в ПО Пам’ять комп’ютера
Пам’ять комп’ютера Разработка автоматизированной системы управления заявками на информационно-технологические услуги
Разработка автоматизированной системы управления заявками на информационно-технологические услуги Аппаратное обеспечение работы компьютера
Аппаратное обеспечение работы компьютера Оценка качества перевода
Оценка качества перевода Построение диаграмм и графиков в электронных таблицах
Построение диаграмм и графиков в электронных таблицах Мониторинг подготовки к ЕГЭ по информатике
Мониторинг подготовки к ЕГЭ по информатике Veeam Replica
Veeam Replica Разработка АИС Клиенті и планирование
Разработка АИС Клиенті и планирование T-SQL, структура программы
T-SQL, структура программы Информационные процессы
Информационные процессы Реляциялық МҚ жобалау жане жобалау кезеңдері
Реляциялық МҚ жобалау жане жобалау кезеңдері