Слайд 2
Слайд 3
1 The description of information security
The global penetration of information technology
into our lives, the gradual transition to electronic ways of doing business set new information security challenges for market participants.
Слайд 4
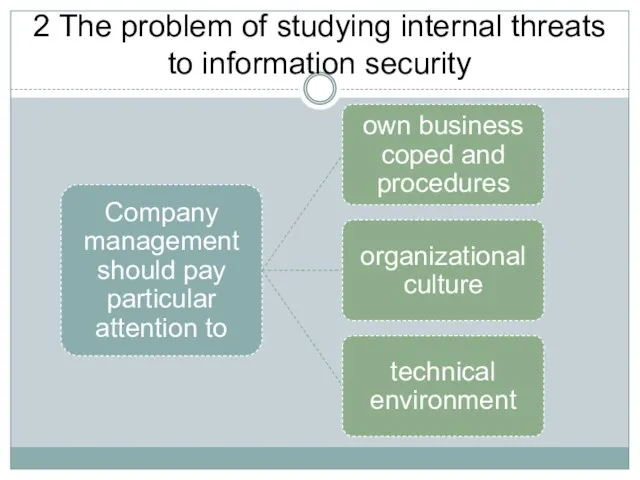
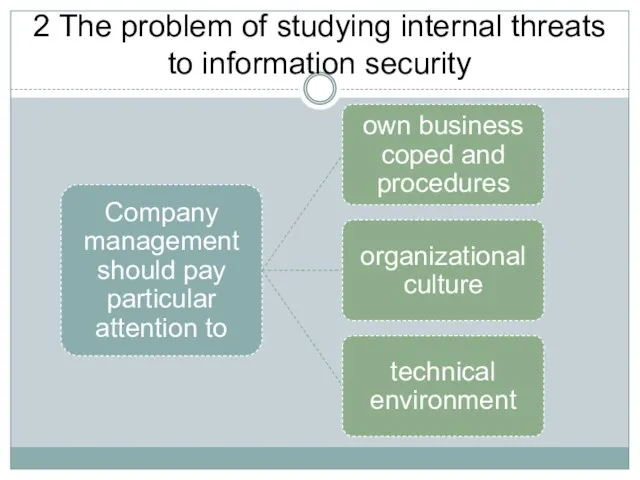
2 The problem of studying internal threats to information security
Слайд 5
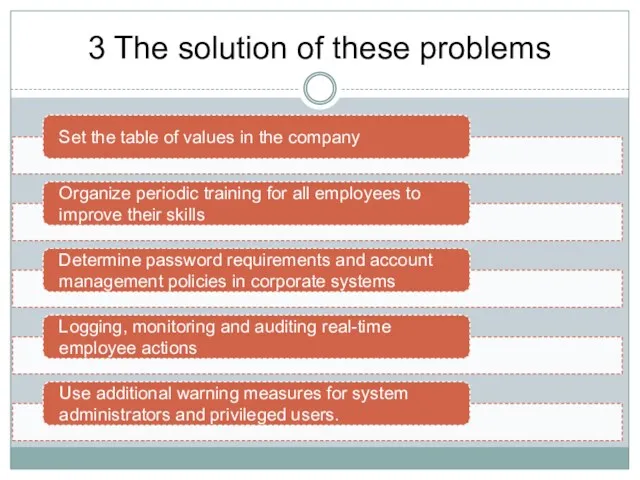
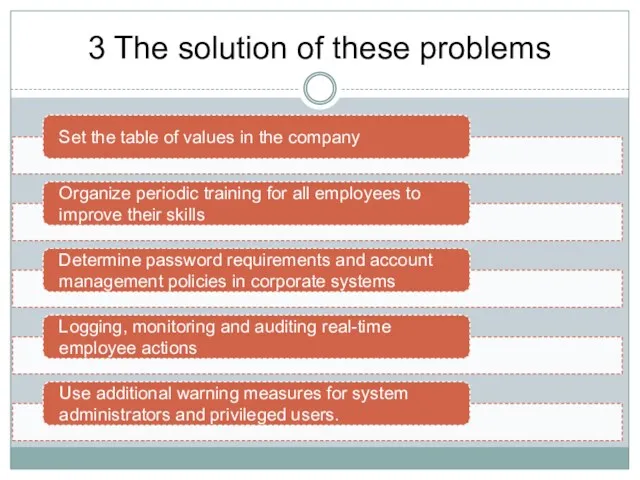
3 The solution of these problems
Слайд 6
Bibliography
1 Belyantsev A.E. Information security as the most important factor in
the state information policy of the Russian Federation // Bulletin of the Academy of Military Sciences. 2015. № 3 (52). Pp. 79-84.
2 Yemelyanov A.A. Experience of implementing information security policies at a small business enterprise in order to ensure information and economic security // Information Security of Russian Regions (IBRD-2015) Conference materials. 2015. p. 213-214.
Krupko A.E. Information security policy: composition, structure, audit of information security of FES // Finance. Economy 2015. No. 8. P. 27-32.
 Инфологическое (концептуальное) моделирование предметной области - подход Oracle
Инфологическое (концептуальное) моделирование предметной области - подход Oracle Встроенные функции, презентация
Встроенные функции, презентация Математические модели потоков телефонных вызовов
Математические модели потоков телефонных вызовов Информационные ресурсы. Этические и правовые нормы информационной деятельности людей.
Информационные ресурсы. Этические и правовые нормы информационной деятельности людей. Кодирование графики
Кодирование графики Основы алгоритмизации и программирования. Объект, его свойства, методы, класс в языке C#
Основы алгоритмизации и программирования. Объект, его свойства, методы, класс в языке C# Интернет-банкинг в России
Интернет-банкинг в России Проектирование БД
Проектирование БД ICT Hardware, Software Requirements
ICT Hardware, Software Requirements Теория игр. Камни
Теория игр. Камни Криминологическая характеристика преступлений против собственности, совершаемых с использованием ИКТ
Криминологическая характеристика преступлений против собственности, совершаемых с использованием ИКТ Завантаження даних з Інтернету
Завантаження даних з Інтернету Об’єкти, функції і події в JavaScript. (Лекція 7)
Об’єкти, функції і події в JavaScript. (Лекція 7) Информационные ресурсы современного общества. Тема 1 (часть 2)
Информационные ресурсы современного общества. Тема 1 (часть 2) React введение
React введение Локальды компьютерлік желілер. Локальды желілердің түрлері
Локальды компьютерлік желілер. Локальды желілердің түрлері Основы Web-дизайна
Основы Web-дизайна Информатика. Введение
Информатика. Введение Язык запросов SQL. Агрегирование и групповые функции. Задачи
Язык запросов SQL. Агрегирование и групповые функции. Задачи CRM-система для управляющих организаций и ТСЖ
CRM-система для управляющих организаций и ТСЖ Введение в безопасность веб-приложений
Введение в безопасность веб-приложений Введение 2022
Введение 2022 Программное обеспечение компьютера. Операционные системы. Файловые системы
Программное обеспечение компьютера. Операционные системы. Файловые системы Кодирование информации. Равномерное кодирование
Кодирование информации. Равномерное кодирование Интернет как инструмент привлечения инвестиций
Интернет как инструмент привлечения инвестиций Системы счисления. Перевод чисел из одной системы счисления в другую систему счисления
Системы счисления. Перевод чисел из одной системы счисления в другую систему счисления Компьютер - универсальная техническая система обработки информации
Компьютер - универсальная техническая система обработки информации Портфолио
Портфолио