Содержание
- 2. Denial-of-service Denial of service (DoS) an action that prevents or impairs the authorized use of networks,
- 3. Classic DoS attacks Flooding ping command Aim of this attack is to overwhelm the capacity of
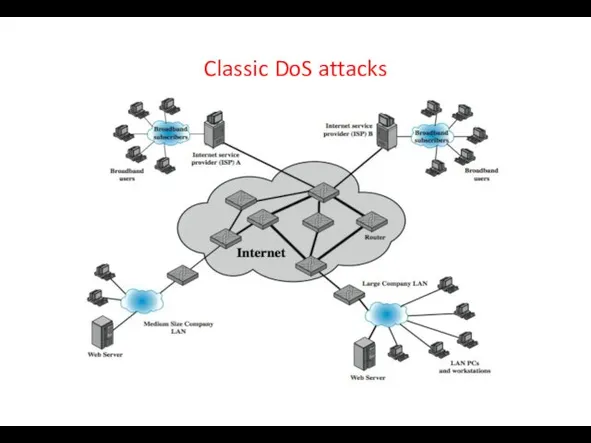
- 4. Classic DoS attacks
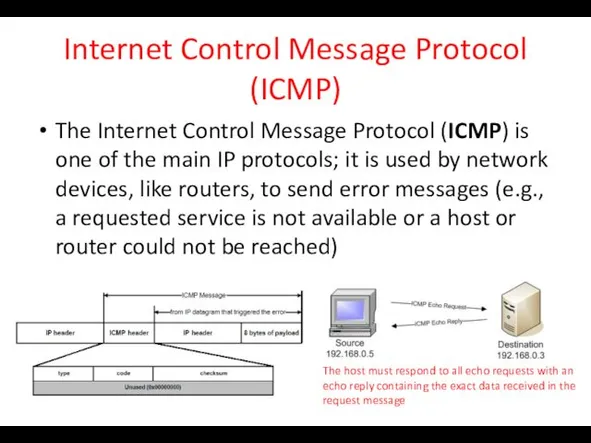
- 5. Internet Control Message Protocol (ICMP) The Internet Control Message Protocol (ICMP) is one of the main
- 6. Source address spoofing Use forged source addresses Usually via the raw socket interface on operating systems
- 7. Backscatter traffic Security researchers (Honeypot Project) advertise blocks of unused IP addresses (no real/legit uses) If
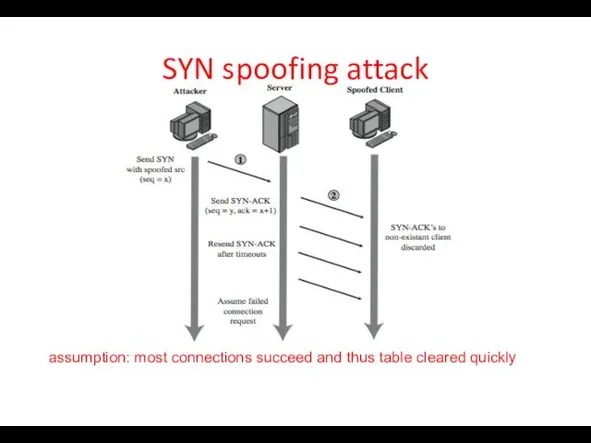
- 8. SYN spoofing Common DoS attack Attacks the ability of a server to respond to future connection
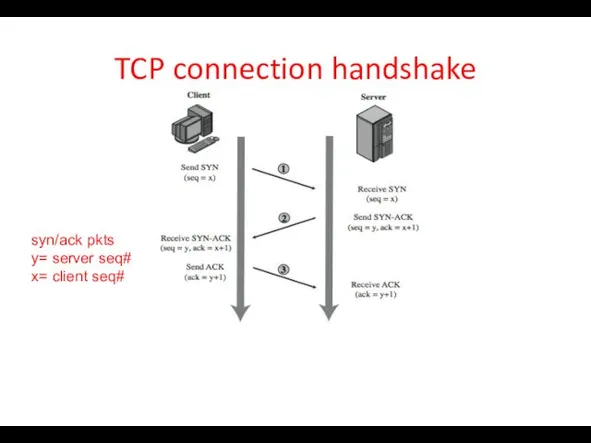
- 9. TCP connection handshake syn/ack pkts y= server seq# x= client seq#
- 10. SYN spoofing attack assumption: most connections succeed and thus table cleared quickly
- 11. SYN spoofing attack: attacker’s source Attacker often uses either random source addresses (addresses that may not
- 12. Types of flooding attacks Classified according to the network protocol used Objective: to overload the network
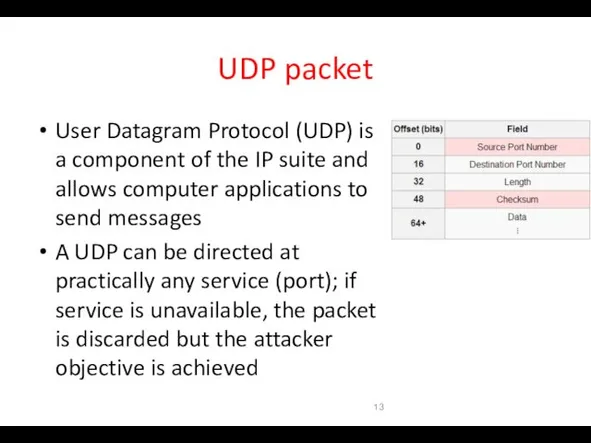
- 13. UDP packet User Datagram Protocol (UDP) is a component of the IP suite and allows computer
- 14. Distributed DoS attacks Have limited volume if single source used Multiple systems allow much higher traffic
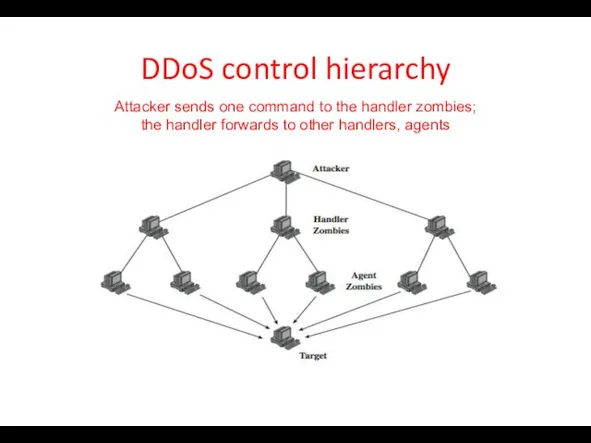
- 15. DDoS control hierarchy Attacker sends one command to the handler zombies; the handler forwards to other
- 16. Application-based bandwidth attacks Force the victim system to execute resource-consuming operations (e.g., searches, complex DB queries)
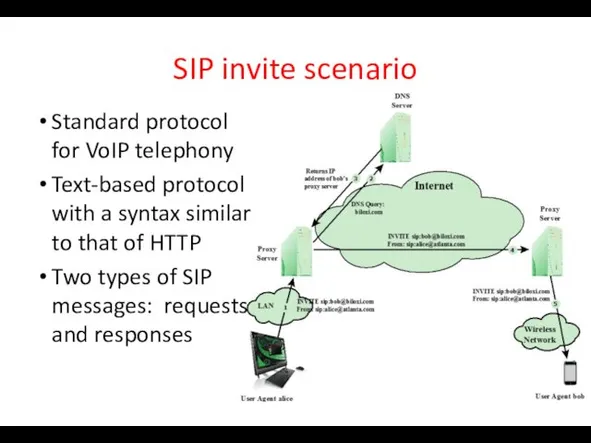
- 17. SIP invite scenario Standard protocol for VoIP telephony Text-based protocol with a syntax similar to that
- 18. HTTP-based attacks Slowloris: On each connection, it sends an incomplete request that does not include the
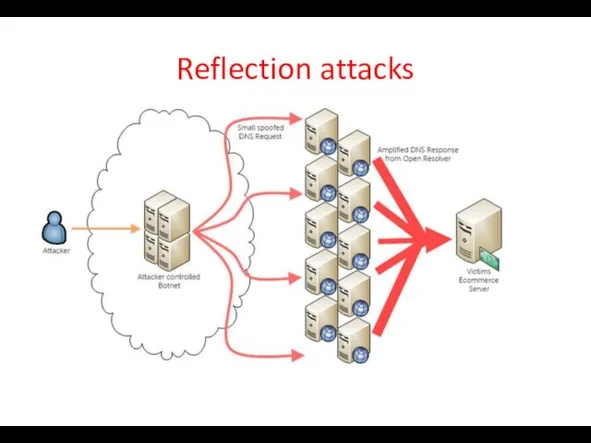
- 19. Reflection attacks Attacker sends packets to a known service on the intermediary with a “spoofed source
- 20. Reflection attacks
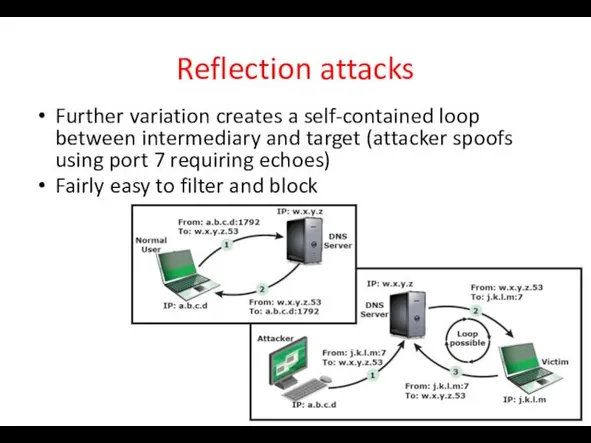
- 21. Reflection attacks Further variation creates a self-contained loop between intermediary and target (attacker spoofs using port
- 22. DNS amplification attacks Use packets directed at a legitimate DNS server as the intermediary system Attacker
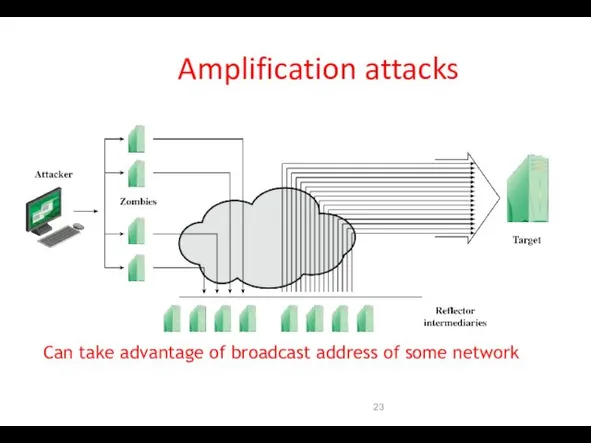
- 23. Amplification attacks Can take advantage of broadcast address of some network
- 24. Four lines of defense against DDoS attacks Attack prevention and preemption (before attack) Attack detection and
- 25. DoS attack prevention Block spoofed source addresses On routers as close to source as possible Filters
- 26. Attack prevention Rate controls in upstream distribution nets On specific packets types e.g. some ICMP, some
- 27. Attack prevention Block IP directed broadcasts Block suspicious services and combinations Manage application attacks with a
- 28. Responding to attacks Good incidence response plan Details on how to contact technical personal for ISP
- 29. Responding to attacks Identify type of attack Capture and analyze packets Design filters to block attack
- 31. Скачать презентацию
 Подання графічних даних. Адитивні та субтрактивні кольори в комп'ютерній графіці
Подання графічних даних. Адитивні та субтрактивні кольори в комп'ютерній графіці Мультиагентная технология (МАТ)
Мультиагентная технология (МАТ) Алгоритм. Алгоритмизация
Алгоритм. Алгоритмизация Алгоритмнің жазылу түрлері
Алгоритмнің жазылу түрлері The site of al Jazeera
The site of al Jazeera Табличные информационные модели. Вычислительные таблицы
Табличные информационные модели. Вычислительные таблицы Комбинированный тип данных. Урок 60. 10 класс
Комбинированный тип данных. Урок 60. 10 класс Программирование разветвляющихся алгоритмов. Начала программирования. Информатика. 8 класс
Программирование разветвляющихся алгоритмов. Начала программирования. Информатика. 8 класс Идентификация. Штриховое кодирование
Идентификация. Штриховое кодирование Технология обработки числовой информации. Электронная таблица MS EXCEL
Технология обработки числовой информации. Электронная таблица MS EXCEL Операции с каталогами
Операции с каталогами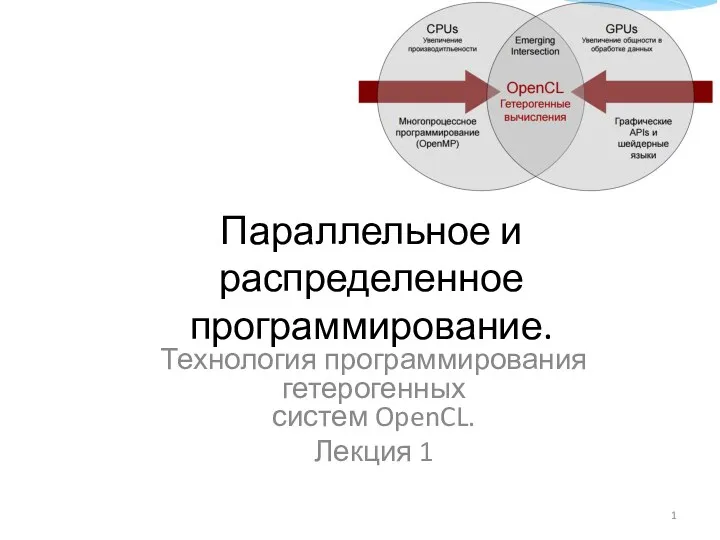 Технология программирования гетерогенных систем OpenCL. Лекция 1
Технология программирования гетерогенных систем OpenCL. Лекция 1 презентация по информатике для 2 класса Алфавит и кодирование информации
презентация по информатике для 2 класса Алфавит и кодирование информации 3. Essential Java Classes 3. Date and Time Home Tasks
3. Essential Java Classes 3. Date and Time Home Tasks Информационные системы. Системы баз данных. Модели данных
Информационные системы. Системы баз данных. Модели данных Әлемнің барлығы Ғаламторда
Әлемнің барлығы Ғаламторда Обзор инструментов обработки Big Data
Обзор инструментов обработки Big Data Программирование на языке Python. Базовый уровень. Модуль 2. Строки и списки. Списки (занятие 4)
Программирование на языке Python. Базовый уровень. Модуль 2. Строки и списки. Списки (занятие 4) Формы и отчеты в СУБД Access
Формы и отчеты в СУБД Access Основы СУБД в ACCESS
Основы СУБД в ACCESS Керування оперативною пам’яттю
Керування оперативною пам’яттю Разработка и форма записи алгоритма и программы
Разработка и форма записи алгоритма и программы Мікроконтролерна система цифрової ідентифікації персоналу для ЧДУ ім. П. Могили
Мікроконтролерна система цифрової ідентифікації персоналу для ЧДУ ім. П. Могили Разработка сайта “Интернет - магазин одежды Dieshh
Разработка сайта “Интернет - магазин одежды Dieshh Презентация Основы информационных технологий
Презентация Основы информационных технологий Программирование (комбинаторика)
Программирование (комбинаторика) Клавиатура компьютера. Основные приемы работы. Виды клавиш и их основное назначение
Клавиатура компьютера. Основные приемы работы. Виды клавиш и их основное назначение Что такое программирование. Язык программирования java
Что такое программирование. Язык программирования java